The Metasploit Framework is an open-source penetration testing and vulnerability assessment tool developed by Rapid7. It provides a robust platform for security professionals, ethical hackers, and researchers to identify, exploit, and validate vulnerabilities in various systems and applications. The Metasploit Framework is designed to assist users in understanding and mitigating security risks through controlled testing and evaluation.
Key Benefits of Metasploit Framework
- Comprehensive Testing: The Metasploit Framework offers a wide array of tools, exploits, payloads, and auxiliary modules that cover a diverse range of systems, applications, and vulnerabilities. This comprehensive toolkit allows users to perform in-depth security assessments.
- Vulnerability Validation: Security professionals can use the Metasploit Framework to verify the existence and severity of vulnerabilities discovered during assessments. This validation helps organizations prioritize and address critical security issues.
- Proactive Defense: By simulating real-world attacks, the framework enables organizations to identify and address vulnerabilities before malicious actors can exploit them. This proactive approach enhances overall security posture.
- Skill Development: The Metasploit Framework serves as a valuable educational tool, allowing security practitioners to learn about exploitation techniques, vulnerability analysis, and mitigation strategies. This hands-on experience contributes to skill development.
- Educational Tool: Metasploit Framework serves as an educational tool, allowing security practitioners to learn about common vulnerabilities, exploit techniques, and defense strategies. It helps individuals understand how attackers think and operate, facilitating better defense strategies.
- Versatility: Metasploit Framework supports a wide range of platforms, operating systems, and applications. It allows penetration testers to target diverse environments, making it a versatile tool for assessing security across different technologies.
- Security Assessment: Metasploit Framework enables security professionals to identify weaknesses in systems and networks before malicious attackers can exploit them. This proactive approach helps organizations improve their security measures and mitigate potential risks.
- Rapid Prototyping: Penetration testers can quickly develop and test proof-of-concept exploits using Metasploit Framework . This is valuable for demonstrating the feasibility of potential attacks and the impact of vulnerabilities.
- Collaborative Community: The framework benefits from a thriving community of security experts who contribute to its development, creating a collective knowledge base for sharing exploits, modules, and improvements. It has a strong and active community of security professionals who contribute to the development of new modules, updates, and improvements. Collaboration within the community enhances the tool's capabilities.
Key Features of Metasploit Framework
- Exploit Modules: Metasploit provides a wide array of pre-built exploit modules for various vulnerabilities. These modules automate the process of testing and exploiting known security weaknesses.
- Payloads: Metasploit includes a collection of payload options that can be used to deliver various types of malicious code to compromised systems. These payloads facilitate different post-exploitation activities.
- Auxiliary Modules: In addition to exploits, the framework provides auxiliary modules for tasks such as scanning, information gathering, and reconnaissance.
- Post-Exploitation: Users can leverage Metasploit for post-exploitation activities, including data extraction, privilege escalation, lateral movement, and maintaining access to compromised systems.
- Resource Scripting: Metasploit supports scripting using various languages, allowing users to automate complex tasks and create custom modules.
- Remote Administration: Metasploit provides capabilities for remote administration, allowing users to control compromised systems from a centralized interface.
- Reporting: The framework offers reporting functionalities that enable users to generate detailed reports on vulnerabilities, successful exploits, and assessment findings.
- Multi-Platform Support: Metasploit is designed to work across multiple platforms, supporting different operating systems and architectures.
- Integration: The framework can be integrated with other security tools and platforms, enhancing the overall effectiveness of security assessments.
- Community Contributions: The Metasploit community contributes to the development of new modules, updates, and improvements, ensuring the tool remains up-to-date and relevant.
- Exploitation Database: Metasploit maintains a vast database of vulnerabilities, exploits, and corresponding data, making it a valuable reference for security practitioners.
The Metasploit Framework's combination of tools, resources, and features makes it an essential component of penetration testing and vulnerability assessment activities. It empowers security professionals to identify and address security weaknesses, bolstering the defense against potential cyber threats. Metasploit Framework is a powerful and widely recognized tool in the field of penetration testing and vulnerability assessment, offering a comprehensive suite of features that aid in identifying, exploiting, and addressing security vulnerabilities.
Setting Up Metasploit Lab Environment
Creating a Metasploit lab environment requires preliminary steps to ensure the setup fulfills or surpasses the system requirements. Adequate preparation of the Metasploit Lab Environment can preemptively address potential issues. It is advisable to utilize a system with the capability to manage multiple virtual machines for hosting the labs effectively. This prudent approach can mitigate future challenges and streamline the learning process with the Metasploit Framework.
Metasploit Framework Hardware Prerequisites
- Storage Space: A minimum of 10 gigabytes of available storage on the host machine is necessary. As the framework employs sizable virtual machines, FAT32 partitions are unsuitable due to their inability to accommodate large files. Opt for NTFS, ext3, or another suitable filesystem format. Recommended space allocation is around 30 gigabytes.
- Memory Allocation: Inadequate memory provisioning for the host machine and guest operating systems can lead to system instability and failure to launch virtual machines. Refer to the following guideline for determining the required RAM:
- Linux “HOST” Minimal Memory Requirements
- 1 GB of system memory (RAM)
- Realistically 2 GB or more
- 1 GB of system memory (RAM)
- Kali “GUEST” Minimal Memory Requirements
- At least 1 GB of RAM (2 GB is recommended) // more never hurts!
- Realistically 2 GB or more with a SWAP file of equal value
- At least 1 GB of RAM (2 GB is recommended) // more never hurts!
- Metasploitable “GUEST” Minimal Memory Requirements
- At least 256 MB of RAM (512 MB is recommended) // more never hurts!
- At least 256 MB of RAM (512 MB is recommended) // more never hurts!
- (Optional) Per Windows “GUEST” Minimal Memory Requirements
- At least 256 MB of RAM (1 GB is recommended) // more never hurts!
- Realistically 1 GB or more with a page file of equal value
- At least 256 MB of RAM (1 GB is recommended) // more never hurts!
- Linux “HOST” Minimal Memory Requirements
- Processor: For optimal performance, a 64-bit quad-core CPU or superior is recommended. While VMware Player's bare minimum requirement is a 400MHz (500MHz recommended) processor, these specifications fall short for the framework's demands. Greater processing power translates to an enhanced experience.
- Internet Connectivity: Establishing the lab mandates downloading substantial virtual machines. Hence, a robust high-speed internet connection is advisable for swift and seamless downloads.
Metasploit Framework Software Prerequisites
- Hypervisor: For optimal compatibility with Kali and Metasploitable, VMware Player is the recommended hypervisor. While VMware Player is accessible for free, registration is mandatory for its download. Virtualization applications and appliances, however, are well worth the registration effort, especially if an account already exists. VMware Workstation and VMware Fusion are alternate options, although neither is free.
Various other hypervisors are available for consideration. Apart from VMware, popular choices include VirtualBox and KVM; however, these options are not discussed here. Installation instructions for Kali Linux are available on the Kali Training site. - Kali Linux: Kali Linux stands as an advanced Linux distribution geared towards Penetration Testing and Security Auditing. It's the designated platform for utilizing the Metasploit Framework. Kali Linux comes pre-loaded with Metasploit and an assortment of other security tools, making it ideal for experimenting against target systems. The latest version of Kali can be acquired at:
https://www.kali.org/get-kali
Once Kali is downloaded, Metasploit can be updated to its latest version within the repositories by executing the following command:
$ apt update && apt upgrade - Metasploitable: An obstacle often encountered while learning to use an exploitation framework is sourcing and configuring targets for scanning and attacking. Thankfully, the Metasploit team recognizes this issue and has introduced "Metasploitable," a deliberately vulnerable VMware virtual machine.
Metasploitable serves as an intentionally vulnerable Linux virtual machine, tailored for security training, tool testing, and the practice of common penetration testing techniques. It operates on recent VMware products and other virtualization technologies like VirtualBox. The image file for Metasploitable 2 can be downloaded from SourceForge.
Caution: Do not expose Metasploitable to untrusted networks; opt for NAT or Host-only mode.
Once the Metasploitable VM is downloaded, extract the zip file, open the .vmx file using your preferred VMware product, and power it on. After a short interval, the system will be up and running, ready for action. The default login credentials are msfadmin:msfadmin.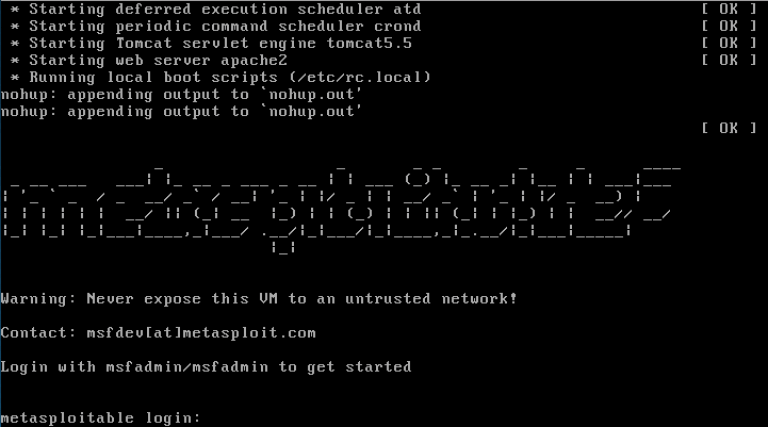
For further VM configuration details, refer to the Metasploitable 2 Exploitability Guide on the Rapid7 website. Beware of potential spoilers in the guide. - Windows: Microsoft provides a collection of downloadable virtual machines designed for testing Microsoft Edge and various versions of Internet Explorer. These VMs prove useful when working with certain exploits and tools within Metasploit. The VMs can be obtained from the following URL:
https://developer.microsoft.com/en-us/windows/downloads/virtual-machines
With the above system requirements met, running tutorials from the Metasploit Unleashed course should proceed without issues.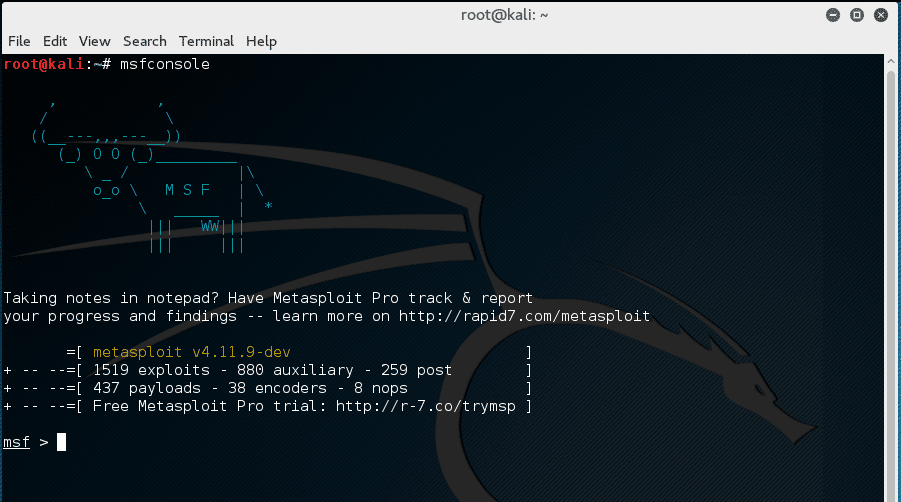
For step-by-step tutorials on how to use Metasploit Framework and take the free full course by visiting the following link:
https://www.offsec.com/metasploit-unleashed/msfconsole
Metasploit Framework Documentation
https://www.kali.org/tools/metasploit-framework