Code signing is a security practice that involves digitally signing software or code to verify its authenticity and integrity. It provides a mechanism for users and systems to verify that the code they receive has not been tampered with or modified by unauthorized parties. Code signing is commonly used in software distribution and execution environments to establish trust and ensure the software's integrity.
When code is signed, a digital signature is applied to the code using a cryptographic algorithm. This signature is generated using the private key of a trusted entity, typically a certificate authority (CA) or the software developer themselves. The digital signature can be verified using the corresponding public key, which is widely distributed and accessible to anyone who wants to verify the code's authenticity.
The process of code signing
Code signing involves the use of digital signatures to verify the authenticity and integrity of software or code.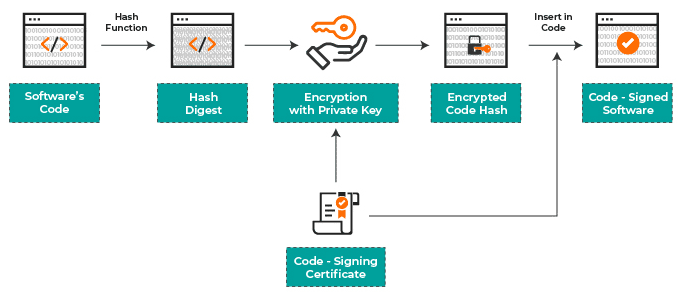
Here's a high-level overview of how code signing works involves the following:
- Certificate Generation: The software developer or organization obtains a digital certificate from a trusted certificate authority (CA). This certificate includes a public key and other identifying information. The certificate is typically valid for a specific period and is associated with the developer or organization.
- Code Preparation: The software or code is prepared for code signing by the developer. This includes compiling the code, performing necessary checks, and ensuring it meets any requirements or standards.
- Digital Signature Creation: Using a code signing tool or platform, the developer generates a digital signature for the code. This involves creating a hash value of the code using a cryptographic algorithm (such as SHA-256) and encrypting the hash with the developer's private key associated with the digital certificate.
- Embedding the Signature: The digital signature is securely embedded within the code or stored in a separate file accompanying the code. This ensures the signature remains associated with the code and cannot be tampered with independently.
- Distribution and Verification: The signed code is distributed to end-users or software distribution platforms. When a user or system encounters the signed code, the digital signature can be verified using the corresponding public key associated with the certificate used for signing.
- Verification Process:The verification process involves several steps:
- The recipient extracts the digital signature from the code.
- The recipient obtains the public key associated with the certificate used for signing. This public key is typically available through the trusted CA or embedded within the code.
- The recipient uses the public key to decrypt and obtain the hash value from the signature.
- The recipient recalculates the hash value of the received code using the same cryptographic algorithm.
- The recalculated hash value is compared to the decrypted hash value from the signature. If they match, the code has not been tampered with since it was signed.
- The recipient extracts the digital signature from the code.
- Trust and Authenticity: If the digital signature is successfully verified, it confirms that the code originated from the trusted developer or organization and has not been modified or tampered with since it was signed. This establishes trust and ensures the authenticity and integrity of the code.
Code signing provides assurance to users that the software or code they receive is genuine, has not been altered, and comes from a trusted source. It helps prevent the distribution and execution of unauthorized or malicious code, enhancing security and trust in software ecosystems.
What is Hash Function?
In code signing, a hash function is used to calculate a unique hash value or message digest of the code being signed. This hash value is then digitally signed using a private key to create a digital signature. The combination of the code's hash value and the digital signature is embedded within the signed code.
Here's how hash functions are utilized in the code signing process:
- Hash Calculation: The code to be signed is processed through a hash function, such as SHA-256 (Secure Hash Algorithm 256-bit), which generates a fixed-size hash value unique to the input code. The hash function produces a compact representation of the code, regardless of its size.
- Hash Verification during Distribution: When users or systems encounter the signed code, they can independently calculate the hash value of the received code using the same hash function. This calculated hash value is compared with the embedded hash value within the digital signature.
- Integrity Check: If the calculated hash value matches the embedded hash value, it confirms that the code has not been modified or tampered with since it was signed. Any changes to the code would result in a different hash value, indicating potential unauthorized alterations.
- Digital Signature Verification: The digital signature accompanying the hash value is verified using the signer's public key. This ensures that the digital signature was applied using the corresponding private key of the signer and verifies the authenticity of the code signer.
By including the hash value of the code in the digital signature, code signing establishes a strong connection between the signed code and its integrity. The hash value acts as a unique identifier and allows recipients to verify that the code has not been tampered with since it was signed by comparing the calculated hash value with the embedded one.
Code signing provides assurance to users that the code originates from a trusted source and has not been modified or compromised. The use of hash functions adds an additional layer of security by ensuring the integrity of the signed code throughout its distribution and execution lifecycle.
What are Code Signing Certificates?
Code signing certificates are digital certificates issued by trusted certificate authorities (CAs) that validate the authenticity and integrity of software or code. These certificates are used to sign executable files, scripts, libraries, drivers, or other types of software code to establish trust and verify the source of the code. Code signing certificates contain several key components:
- Public Key: The certificate includes a public key that corresponds to the private key held by the code signing entity. The public key is used by recipients to verify the digital signatures applied to the code.
- Digital Signature: The certificate incorporates a digital signature generated using the private key of the code signing entity. This signature is applied to the code, ensuring its integrity and providing proof of the signer's identity.
- Issuer Information: The certificate includes information about the CA that issued the certificate, such as the CA's name, digital signature, and certificate validity period. This information helps establish trust in the certificate itself.
- Subject Information: The certificate also includes details about the entity that requested the certificate, such as the organization name, email address, and other identifying information. This information provides further validation of the signer's identity.
When code is signed using a code signing certificate, the digital signature acts as a tamper-evident seal. It allows users or systems to verify that the code has not been modified since it was signed and that it comes from a trusted source. By verifying the digital signature against the corresponding public key, recipients can establish trust and assurance in the authenticity and integrity of the signed code.
Code signing certificates are typically issued for a specified duration, and they need to be renewed periodically to ensure continued trust and validity. Organizations or developers obtain code signing certificates from trusted CAs, which have established processes for verifying the identity and authenticity of the certificate requestors.
The use of code signing certificates is prevalent in various software ecosystems, including operating systems, web browsers, mobile platforms, and application marketplaces. It helps protect users from unauthorized or malicious code, enhances software security, and establishes trust between software developers and users.
What is Public Key Encryption?
Public key encryption, also known as asymmetric encryption, is a cryptographic method that uses two related keys: a public key and a private key. These key pairs are mathematically linked, but the private key is kept secret, while the public key is shared openly.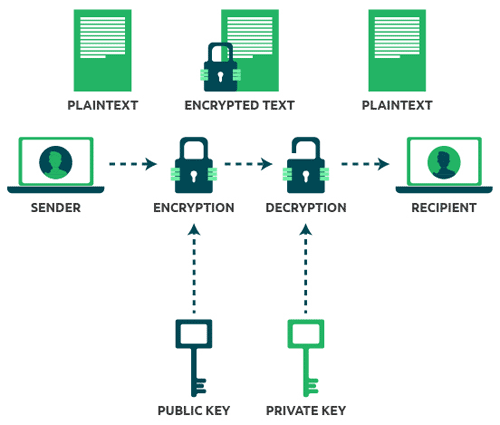
Here's how public key encryption works:
- Key Generation:
- A user generates a key pair consisting of a public key and a private key.
- The private key is kept securely and should never be shared with others.
- The public key is made widely available to anyone who needs to encrypt data or verify digital signatures.
- A user generates a key pair consisting of a public key and a private key.
- Encryption:
- To encrypt a message or data, the sender uses the recipient's public key.
- The sender performs encryption operations on the plaintext using the recipient's public key, transforming it into ciphertext.
- The ciphertext is transmitted to the recipient.
- To encrypt a message or data, the sender uses the recipient's public key.
- Decryption:
- The recipient, using their private key, decrypts the received ciphertext to obtain the original plaintext message.
- Decryption involves performing mathematical operations on the ciphertext using the recipient's private key, which yields the original message.
- The recipient, using their private key, decrypts the received ciphertext to obtain the original plaintext message.
Key aspects of public key encryption:
- Security: The strength of public key encryption lies in the difficulty of deriving the private key from the public key. Even if the public key is known, it should be computationally infeasible to determine the private key.
- Confidentiality: Public key encryption ensures that only the intended recipient possessing the private key can decrypt the encrypted message and access the original plaintext.
- Digital Signatures: Public key encryption can also be used to create digital signatures. The sender uses their private key to sign a message, and the recipient can verify the signature using the sender's public key. This provides integrity and non-repudiation, ensuring that the message originated from the sender and was not altered in transit.
- Key Exchange: Public key encryption also enables secure key exchange between parties. By encrypting a symmetric encryption key with the recipient's public key, secure communication using symmetric encryption can be established.
Public key encryption algorithms include RSA (Rivest-Shamir-Adleman), Elliptic Curve Cryptography (ECC), and Diffie-Hellman (DH) key exchange. These algorithms provide the foundation for secure communication, data protection, and digital signatures in various applications, including secure messaging, e-commerce, and secure network communications.
How to Secure the Code Signing Process?
Securing the code signing process is crucial to maintain the integrity and trustworthiness of signed code. Here are some best practices to enhance the security of the code signing process:
- Secure Private Keys: Protect the private keys associated with code signing certificates. Store them in secure, encrypted locations, such as Hardware Security Modules (HSMs) or dedicated cryptographic devices. Use strong passwords or passphrases to protect private keys and limit access to authorized personnel only.
- Implement Two-Factor Authentication: Enable two-factor authentication (2FA) for accessing code signing infrastructure and platforms. Require additional authentication factors, such as smart cards, hardware tokens, or biometrics, to prevent unauthorized access.
- Secure Build Environment: Ensure the security of the build environment used for code signing. Protect the build systems from malware, unauthorized access, and compromise. Regularly update software, apply security patches, and use reputable security tools to scan for vulnerabilities.
- Code Integrity Checks: Implement measures to verify the integrity of the code before signing. This includes using version control systems, secure repositories, and automated build processes to ensure the code has not been tampered with or modified during development.
- Certificate Authority (CA) Selection: Obtain code signing certificates from reputable and trusted CAs. Research and choose CAs that follow industry best practices, have a strong track record, and employ stringent validation processes to issue certificates.
- Certificate Expiration Management: Establish processes for managing certificate expiration. Regularly monitor and renew code signing certificates before they expire to avoid disruptions in the signing process. Maintain an inventory of certificates and their expiration dates to ensure timely renewal.
- Code Signing Infrastructure Protection: Protect the code signing infrastructure from unauthorized access and tampering. Implement firewalls, intrusion detection systems, and strong access controls to secure the systems used for code signing.
- Code Signing Policy and Procedures: Develop and enforce a code signing policy that outlines the procedures, roles, responsibilities, and security controls for the code signing process. Regularly review and update the policy to align with industry best practices and changing security requirements.
- Code Signing Audit and Logging: Implement logging and monitoring mechanisms to track code signing activities. Maintain audit logs of code signing operations, including details such as signing requests, signing authorities, and timestamps. Regularly review logs to detect any suspicious activities or anomalies.
- Ongoing Education and Awareness: Train developers, administrators, and other personnel involved in the code signing process on security best practices. Raise awareness about the importance of code signing security, the risks of unauthorized signing, and the need to follow secure coding practices.
By implementing these security measures, organizations can significantly enhance the security of their code signing process, safeguard the integrity of signed code, and maintain trust with users and stakeholders.
The benefits of code signing include:
- Authenticity: Code signing provides assurance that the software or code originates from a trusted source, ensuring its authenticity.
- Integrity: The digital signature allows recipients to verify that the code has not been altered or modified since it was signed, providing integrity assurance.
- Trust and Reputation: Code signing helps establish trust between software developers and users, as users can verify the integrity of the code and the identity of the signer.
- Protection against Malware: Code signing can help protect against the distribution and execution of malicious or tampered code by providing an additional layer of security and verification.
Code signing is commonly used in operating systems, software applications, mobile apps, and other digital environments to establish trust, protect users, and maintain the integrity of software distribution and execution.
Code Signing Tools
There are several reputable code signing technologies and platforms available in the market. The best code signing technologies can vary based on specific requirements, platform compatibility, and industry standards. Here are some popular code signing technologies:
- Java Code Signing: Java applications and applets can be signed using Java code signing technologies. This helps establish trust when executing Java-based software, especially in web-based environments.
- Platforms: Java applications and applets
- Benefits:
- Trusted execution: Signed Java code provides assurance that the application or applet has not been modified since it was signed, improving security.
- Applet compatibility: Signed applets have fewer restrictions when running in a web browser, avoiding security warnings and allowing full functionality.
- Establishes trust: Signed Java applications and applets are more likely to be trusted by users and systems, enhancing reputation and adoption.
- Trusted execution: Signed Java code provides assurance that the application or applet has not been modified since it was signed, improving security.
- Platforms: Java applications and applets
- Microsoft Authenticode: Microsoft Authenticode is a widely used code signing technology for Windows platforms. It allows developers to digitally sign Windows executables, libraries (DLLs), installation packages (MSI files), and other types of Windows software.
- Platform: Windows
- Benefits:
- Establishes trust: Authenticode provides assurance to users that the software or code comes from a trusted source and has not been tampered with since it was signed.
- Smoother installation experience: Authenticode-signed software avoids security warnings and prompts during installation, improving the user experience.
- Enhanced security: Authenticode helps protect against the distribution and execution of unauthorized or malicious software.
- Establishes trust: Authenticode provides assurance to users that the software or code comes from a trusted source and has not been tampered with since it was signed.
- Platform: Windows
- Apple Developer ID: Apple Developer ID is the code signing technology for macOS and iOS applications. It enables developers to sign their software using Apple-issued certificates, ensuring the authenticity and integrity of their apps distributed through the Apple App Store or other distribution channels.
- Platforms: macOS, iOS
- Benefits:
- App Store distribution: Developer ID-signed apps can be distributed through the Apple App Store, reaching a wide user base.
- Trusted app execution: Developer ID ensures that apps are signed by trusted developers, reducing the risk of unauthorized or tampered apps.
- Enhanced security: Developer ID-signed apps are validated by Apple, reducing the risk of malware or untrusted software.
- App Store distribution: Developer ID-signed apps can be distributed through the Apple App Store, reaching a wide user base.
- Platforms: macOS, iOS
- Android App Signing: Android developers can sign their apps using Android app signing technologies, which involve generating a private key and signing the APK (Android Application Package) files. This verifies the authenticity and integrity of Android apps.
- Platform: Android
- Benefits:
- Trusted app distribution: Android app signing ensures that apps come from a verified source, enhancing trust and reducing the risk of unauthorized or tampered apps.
- Seamless updates: App signing allows developers to distribute updates to their apps without requiring users to uninstall and reinstall, simplifying the update process.
- Enhanced security: Signed apps are verified by the Android platform, reducing the risk of malicious or untrusted software.
- Trusted app distribution: Android app signing ensures that apps come from a verified source, enhancing trust and reducing the risk of unauthorized or tampered apps.
- Platform: Android
- Mozilla Add-on Signing: Mozilla Add-on Signing is the code signing mechanism for Firefox browser extensions and add-ons. It ensures that extensions are reviewed and signed by Mozilla, reducing the risk of malicious or untrusted add-ons.
- Platform: Mozilla Firefox browser extensions and add-ons
- Benefits:
- Enhanced security: Signed add-ons are reviewed and signed by Mozilla, reducing the risk of malicious or untrusted extensions.
- Better user experience: Signed add-ons can be installed without triggering security warnings or prompts, improving the user experience.
- Trust and reputation: Signed add-ons are more likely to be trusted by users, enhancing the reputation of the developer and the add-on.
- Enhanced security: Signed add-ons are reviewed and signed by Mozilla, reducing the risk of malicious or untrusted extensions.
- Platform: Mozilla Firefox browser extensions and add-ons
- Adobe AIR Code Signing: Adobe AIR applications can be digitally signed to assure users that the application comes from a trusted source and has not been tampered with.
- Platform: Adobe AIR applications
- Benefits:
- Establishes trust: Code signing assures users that the Adobe AIR application comes from a trusted source and has not been tampered with.
- Enhanced user experience: Signed AIR applications can be installed seamlessly without security warnings or prompts.
- Security and integrity: Code signing helps protect against the distribution of malicious or unauthorized AIR applications.
- Establishes trust: Code signing assures users that the Adobe AIR application comes from a trusted source and has not been tampered with.
- Platform: Adobe AIR applications
The benefits highlight the significance of code signing technologies in establishing trust, enhancing security, and providing a smooth user experience in different software ecosystems. It's important to follow the specific guidelines and requirements provided by each platform or technology vendor to maximize the benefits and ensure compliance.
When selecting a code signing technology, it is important to consider factors such as platform compatibility, industry standards, reputation, and the level of trust associated with the signing technology. Additionally, it's advisable to follow the guidelines and recommendations provided by the respective platform or operating system vendor to ensure compliance with their code signing requirements.
References:
https://en.wikipedia.org/wiki/Code_signing
https://developer.apple.com/support/code-signing
https://www.computer.org/publications/tech-news/trends/what-is-a-code-signing-certificate