Vulnerability scoring systems such as CVSS, CVE, CWE, and EPSS are methods or frameworks used to assess and quantify the severity and potential impact of security vulnerabilities in software, hardware, or systems. These scoring systems provide a way to prioritize and address vulnerabilities based on their perceived risk and criticality. They are commonly used by organizations, security researchers, and software vendors to categorize vulnerabilities, allowing them to allocate resources efficiently for mitigation efforts.
Key benefits and aspects of Vulnerability Scoring Systems
- Risk Prioritization: Vulnerability scoring systems help organizations prioritize their response to vulnerabilities by quantifying their severity or risk. This allows security teams to focus on addressing the most critical issues first.
- Resource Allocation: By assigning scores or ratings to vulnerabilities, these systems help organizations allocate their limited resources more effectively. They can allocate resources to address vulnerabilities that pose the greatest risk to their systems and data.
- Consistency: Vulnerability scoring systems provide a consistent and objective way to evaluate vulnerabilities. This consistency is especially valuable when dealing with a large number of vulnerabilities across diverse systems and applications.
- Communication: Scoring systems facilitate communication among different stakeholders, including security teams, IT departments, and management. They provide a common language for discussing the severity of vulnerabilities and the urgency of remediation.
- Mitigation Guidance: Many scoring systems offer guidance on how to mitigate or remediate vulnerabilities. This helps organizations take appropriate actions to reduce the risk associated with each vulnerability.
- Vendor and Product Neutrality: Scoring systems are typically vendor-neutral and can be applied to vulnerabilities in various products and technologies. This neutrality ensures that organizations can use the same system regardless of their technology stack.
- Severity Metrics: Vulnerability scoring systems use severity metrics to assess the potential impact of a vulnerability. These metrics often consider factors like the ease of exploitation, potential consequences, and the scope of the vulnerability's impact.
- Scoring Scales: Different scoring systems use various scales or numerical ranges to represent vulnerability severity. For example, the Common Vulnerability Scoring System (CVSS) uses a scale from 0 to 10, with 10 being the most severe.
- Base, Temporal, and Environmental Metrics: Some scoring systems break down the assessment into different categories. For example, CVSS includes base metrics (inherent qualities of the vulnerability), temporal metrics (factors that change over time), and environmental metrics (factors specific to the organization's environment).
- Public Databases: Many vulnerability scoring systems are associated with public databases, such as the Common Vulnerabilities and Exposures (CVE) database. These databases provide a central repository of vulnerability information and assign unique identifiers to each vulnerability.
- Ongoing Updates: Vulnerability scoring systems evolve over time to adapt to new threats and vulnerabilities. Updates may include changes to scoring formulas, additional metrics, or refinements to the assessment process.
- Integration: Scoring systems can be integrated into vulnerability management tools and security information and event management (SIEM) systems. This integration streamlines the vulnerability assessment and remediation process.
- Community Involvement: Some scoring systems involve the cybersecurity community in their development and maintenance. This collaborative approach ensures that scoring systems remain relevant and effective.
In summary, vulnerability scoring systems offer several key benefits, including risk prioritization, resource allocation, consistency, and communication, while covering various aspects such as severity metrics, scoring scales, and ongoing updates. These systems play a crucial role in modern cybersecurity practices.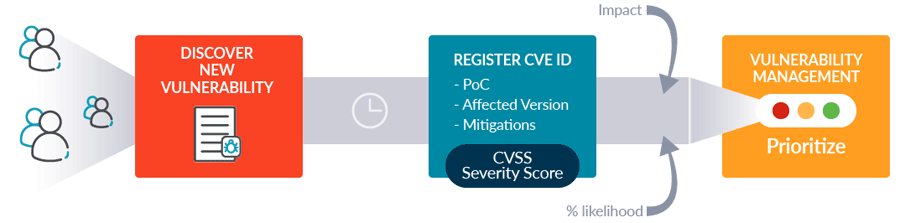
Four most well-known Vulnerability Scoring Systems
- Common Vulnerability Scoring System (CVSS):
- Purpose: CVSS is a widely used open standard for assessing and rating the severity of vulnerabilities. It provides a consistent and objective way to evaluate the impact of security flaws.
- Components: CVSS calculates a numerical score based on several metrics, including:
- Base Metrics: These assess the intrinsic qualities of a vulnerability, such as how it's accessed, its impact on confidentiality, integrity, and availability, and other factors.
- Temporal Metrics: These capture the characteristics of a vulnerability that may change over time, like the availability of patches or the prevalence of exploits.
- Environmental Metrics: These consider factors specific to an organization's environment, like the importance of the affected asset.
- Scoring: CVSS produces a score typically ranging from 0.0 (no impact) to 10.0 (severe impact). This score helps organizations prioritize which vulnerabilities to address first. The score is divided into severity levels, such as Low, Medium, High, and Critical.
- Use Cases: CVSS scores are commonly used by security teams, vulnerability management programs, and organizations to prioritize patching and mitigation efforts.
- Common Vulnerability and Exposure (CVE):
- Purpose: CVE is a system for identifying, naming, and tracking individual security vulnerabilities in software and hardware. It does not assign severity scores directly but provides a standardized identifier for each vulnerability.
- Components: CVE entries include a unique CVE identifier, a description of the vulnerability, references to additional information, and information about affected products and versions.
- Scoring: CVE itself does not provide severity scores. However, it is often used alongside scoring systems like CVSS to provide a complete picture of a vulnerability, including its name, description, and severity score.
- Use Cases: CVE is used as a reference system to uniquely identify vulnerabilities across the cybersecurity community. Security analysts, researchers, and organizations use CVE identifiers to discuss, track, and report vulnerabilities.
- Common Weakness Enumeration (CWE):
- Purpose: CWE is a community-driven project that provides a comprehensive list of common software security weaknesses or vulnerabilities. Unlike CVSS or CVE, CWE does not assign scores to vulnerabilities. Instead, it focuses on identifying and describing the various types of weaknesses that can exist in software.
- Components: CWE categorizes weaknesses into different classes, each with a unique identifier. It provides detailed descriptions of these weaknesses, along with examples and guidance on how to prevent or mitigate them. It acts as a knowledge base for understanding the root causes of vulnerabilities.
- Use Cases: CWE is widely used by security professionals, software developers, and organizations to:
- Enhance secure coding practices by educating developers about common pitfalls.
- Perform security assessments and code reviews to identify and rectify vulnerabilities.
- Improve the design and development of software and systems to prevent vulnerabilities in the first place.
- Communicate effectively about security weaknesses within the cybersecurity community.
- Exploit Prediction Scoring System (EPSS):
- Purpose: The Exploit Prediction Scoring System is designed to assess the likelihood that a known vulnerability will be exploited by attackers in the near future. Unlike CVSS, which focuses on the severity of vulnerabilities, EPSS looks at the risk of actual exploitation.
- Components: EPSS takes into account various factors to predict the likelihood of exploitation, including the availability of exploit code, historical data on exploits, and the attractiveness of the target system to attackers.
- Scoring: EPSS typically provides a score or rating that reflects the risk of exploitation. Higher scores indicate a higher likelihood of exploitation, while lower scores suggest a lower risk.
- Use Cases: EPSS is used by security teams and organizations to:
- Prioritize the patching or mitigation of vulnerabilities that are most likely to be targeted by attackers.
- Allocate resources and focus efforts on vulnerabilities that pose an imminent threat.
- Make informed decisions about when and how to apply security updates.
These scoring systems help security professionals and organizations make informed decisions about how to allocate resources to address vulnerabilities. They are essential tools in the field of cybersecurity, enabling a more systematic and structured approach to vulnerability management and mitigation.
To learn more about Vulnerability Scoring Systems, visit the following links:
https://nvd.nist.gov
https://www.cve.org
https://cwe.mitre.org
https://www.first.org/cvss
https://www.first.org/epss