Core Impact is a commercial penetration testing tool developed by Core Security, a HelpSystems Company. It is designed to assess the security of systems, networks, and applications by simulating real-world cyberattacks. Core Impact provides a comprehensive set of tools and features to help security professionals identify vulnerabilities, test the effectiveness of defenses, and prioritize remediation efforts.
Key Benefits of Core Impact
- Advanced Penetration Testing: Core Impact offers advanced capabilities for simulating sophisticated cyberattacks, allowing security professionals to replicate real-world threat scenarios and evaluate the resilience of their systems.
- Comprehensive Coverage: The tool covers a wide range of attack vectors and vulnerabilities, including network exploitation, web application vulnerabilities, client-side attacks, social engineering, and more.
- Customizable Testing: Core Impact provides the flexibility to customize and create tailored penetration testing scenarios based on specific requirements and target environments.
- Automation and Workflow: The tool supports automation of complex attack sequences, helping security teams save time and effort by automating repetitive tasks and processes.
- Real-time Reporting: Core Impact offers detailed and actionable reports that provide insights into vulnerabilities, potential impact, and recommended remediation steps. These reports aid in communication with stakeholders and prioritizing security improvements.
- Exploit Validation: Core Impact goes beyond vulnerability scanning by validating the exploitation of vulnerabilities, providing assurance that identified vulnerabilities are indeed exploitable.
Key Features of Core Impact
- Exploitation: Core Impact includes a vast collection of pre-built exploits, payloads, and attack techniques to target various operating systems, applications, and network devices.
- Web Application Testing: The tool supports testing web applications for security vulnerabilities, including SQL injection, Cross-Site Scripting (XSS), and other common web application vulnerabilities.
- Social Engineering: Core Impact includes social engineering capabilities to test the human element of security by simulating phishing campaigns and other social engineering attacks.
- Client-side Attacks: The tool can simulate attacks that target end-user systems through malicious documents, browser exploits, and other client-side vulnerabilities.
- Network Exploitation: Core Impact supports network penetration testing by identifying and exploiting vulnerabilities in network services, protocols, and devices.
- Wireless Assessment: The tool can assess wireless network security by identifying vulnerabilities in Wi-Fi networks and devices.
- Reporting and Collaboration: Core Impact generates detailed reports that provide a clear overview of vulnerabilities, exploited systems, and recommended actions. It supports collaboration by enabling the sharing of results and insights with team members.
- Integration: Core Impact can be integrated with other security tools and solutions to streamline workflows and enhance overall security operations.
Core Impact is used by security professionals, penetration testers, and ethical hackers to identify security weaknesses, assess risks, and validate security measures within organizations. Its advanced capabilities, comprehensive coverage, and extensive reporting make it a valuable asset in performing thorough and realistic security assessments.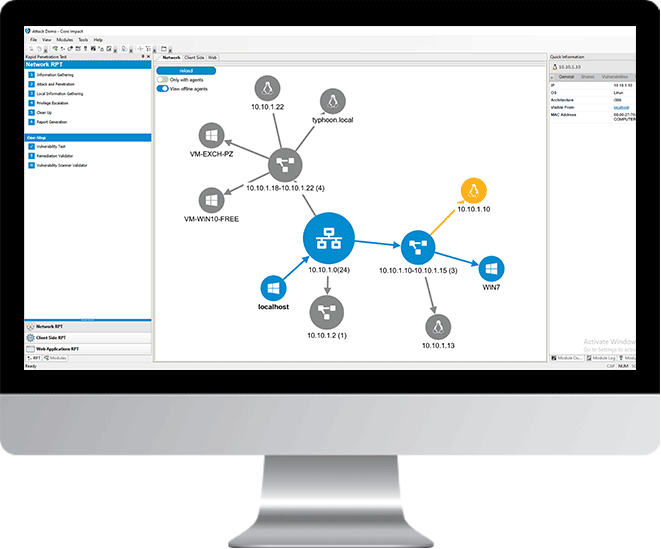
Installing Core Impact
- Download: Use the links below to download the latest version of Core Impact.
https://www.coresecurity.com/products/core-impact/trial-download - Install: Run the installer and launch Core Impact.
- Start exploring Core Impact: Completely new to Core Impact?
Watch a demo: https://www.coresecurity.com/products/core-impact/demo-watch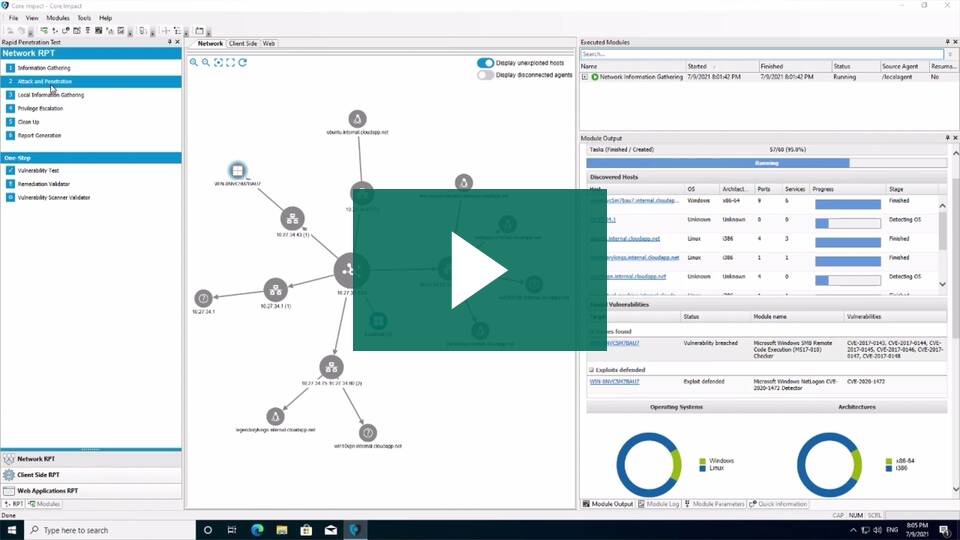
For more information and tutorials, visit the following link:
https://www.coresecurity.com/products/core-impact