Network security encompasses a wide range of practices, policies, and technologies that work together to protect computer networks and their resources from unauthorized access, misuse, modification, or disruption. Its primary objective is to ensure the confidentiality, integrity, and availability (CIA) of network resources by securing the network infrastructure, devices, and data transmission within a network. The primary goal of network security is to prevent unauthorized access to sensitive information and protect network resources from various threats, including cyberattacks, malware, data breaches, and unauthorized network access.
To achieve network security, various components and practices are employed, including:
- Firewalls: Acting as a barrier between trusted internal networks and untrusted external networks, firewalls enforce predefined security policies to control and filter network traffic.
- Hardware Firewalls: Hardware firewalls, also known as network-based firewalls, are physical devices with their own processing power. They act as a barrier between trusted internal networks and untrusted external networks, such as the internet. They filter network packets and traffic requests from untrusted sources. Hardware firewalls are ideal for businesses with numerous devices and can be deployed as external or internal firewalls. However, they may not provide comprehensive endpoint security and a combination of software and hardware firewalls is recommended for optimal network security.
- Software Firewalls: Software firewalls, or host-based firewalls, are installed independently on each device. They offer more granular control, allowing access to specific applications while denying others. Software firewalls can create defense in depth by separating individual network endpoints. However, they can be resource-intensive and difficult to manage in large organizations, requiring separate configuration and maintenance for each device.
- Cloud Firewalls: Cloud-based firewalls, also known as firewall as a service (FaaS), are offered by managed security service providers. They can monitor internal network traffic and third-party on-demand environments. Cloud firewalls are scalable, cost-effective, and provide perimeter security for internal networks or cloud infrastructures. However, there may be a loss of control over security assets and potential compatibility issues when migrating to a new cloud provider.
- Packet-Filtering Firewalls: Packet filtering firewalls are the simplest type of firewall that examines data packets based on source and destination IP addresses, protocol, and port. They are quick, inexpensive, and effective but offer rudimentary security and cannot inspect the content of data packets, making them vulnerable to certain types of attacks.
- Proxy Firewalls: Proxy firewalls, or application-level gateways, use a proxy server at the application layer. They establish the connection between external clients and internal devices, providing privacy and security. Proxy firewalls inspect data packets using stateful and deep packet inspection, making decisions based on predefined criteria. They restrict direct connections between internal and external networks but can introduce delays and may not support all network protocols.
- Next-Generation Firewalls (NGFW): Next-generation firewalls go beyond traditional firewalls by adding application-level inspection, intrusion prevention, and intelligence from outside the firewall. NGFWs perform deep packet inspection, detect malware, and provide comprehensive network security. They can incorporate other security solutions and offer advanced features like DDoS attack prevention and decryption functionality for encrypted applications. NGFWs are more expensive and may require integration with other security systems.
- Threat-Focused NGFW: Threat-focused NGFWs include all the features of regular NGFWs and offer advanced threat detection and mitigation services. They employ intelligent security automation and retrospective security measures to respond quickly to attacks and reduce the time from threat detection to cleanup.
- Stateful Inspection Firewalls: Stateful inspection firewalls combine packet inspection with the tracking of established connections, providing stronger security. They create a state table to enable predicted incoming network traffic. Stateful firewalls have extensive logging capabilities but require more system resources and may reduce network speed.
- Circuit-Level Gateways: Circuit-level gateways work at the session layer, verifying established TCP connections. They are cost-effective, easy to install and manage, and have minimal impact on network performance. However, they cannot inspect data packet content and should be used in conjunction with other firewalls for enhanced security.
- Unified Threat Management (UTM) Firewalls: UTM appliances offer a comprehensive security solution for small and medium-sized businesses. They combine traditional firewall functionality with additional features like intrusion detection and web application firewall capabilities. UTMs are designed for simplicity and ease of use but may not provide the highest level of security in each individual security function.
- Web application firewall (WAF): A web application firewall (WAF) safeguards web applications by monitoring and filtering HTTP traffic between the application and the Internet. It protects against various threats such as cross-site forgery, cross-site scripting (XSS), file inclusion, and SQL injection. A WAF operates at the protocol layer 7 in the OSI model and is not designed to protect against all types of attacks. Typically, it is part of a comprehensive security suite that combines multiple technologies to provide a robust defense against different attack vectors. By deploying a WAF in front of a web application, it is shielded from direct exposure to the Internet. Acting as a reverse proxy, the WAF ensures that clients must pass through it before reaching the server, providing an additional layer of protection and preserving the server's anonymity.
- Hardware Firewalls: Hardware firewalls, also known as network-based firewalls, are physical devices with their own processing power. They act as a barrier between trusted internal networks and untrusted external networks, such as the internet. They filter network packets and traffic requests from untrusted sources. Hardware firewalls are ideal for businesses with numerous devices and can be deployed as external or internal firewalls. However, they may not provide comprehensive endpoint security and a combination of software and hardware firewalls is recommended for optimal network security.
- Antivirus Software: Antivirus software scans and detects malicious software (malware) to prevent its execution and protect against potential threats.
- Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): IDS monitors network traffic, identifying potential threats, while IPS takes real-time action to prevent and block such threats.
- Intrusion Prevention Systems (IPS): Intrusion Prevention Systems (IPS) are security systems that actively take action to prevent harmful behavior when detected on a network. They go beyond just identifying threats, such as reporting or alerting, and instead take measures to block or drop the malicious activity. IPS can be implemented through both hardware and software solutions.
While Intrusion Detection Systems (IDS) solely identify harmful behavior without taking action, IPS is an enhanced solution commonly integrated as an optional component in next-generation firewalls and unified threat management (UTM) solutions. To ensure optimal network performance, IPS must be capable of efficiently scanning high volumes of traffic without causing significant slowdowns, similar to other network security systems. - Host-based Intrusion Detection Systems (HIDS): Host-based Intrusion Detection Systems (HIDS) are programs that monitor individual computers or networks for any unusual behavior, such as external intrusions or internal misuse of resources and data. Similar to a home security system, HIDS software tracks and alerts network administrators of abnormal activities. When utilizing HIDS tools, administrators can easily search through log files created by applications to identify indicators of intrusion or other irregularities. The primary purpose of HIDS tools is automated detection, eliminating the need for manual searching through log files once they have been sorted and processed.
- Network-based Intrusion Detection Systems (NIDS): Network-based Intrusion Detection Systems (NIDS) are deployed throughout a network in an intelligent manner to passively monitor the traffic flowing through them. NIDS can be implemented as hardware or software systems and can connect to various network media, including Ethernet and FDDI, depending on the system manufacturer. These systems typically feature two network ports and perform functions such as promiscuous mode listening, control, and reporting.
- Intrusion Prevention Systems (IPS): Intrusion Prevention Systems (IPS) are security systems that actively take action to prevent harmful behavior when detected on a network. They go beyond just identifying threats, such as reporting or alerting, and instead take measures to block or drop the malicious activity. IPS can be implemented through both hardware and software solutions.
- Unified Threat Management (UTM): UTM consolidates multiple security features such as firewall, antivirus, intrusion detection and prevention, and content filtering into a single device, providing comprehensive network security.
- Wireless Intrusion Prevention and Detection System (WIDPS): WIDPS monitors wireless networks for unauthorized access and potential attacks, ensuring the security of wireless communications.
- Network Access Control (NAC): NAC verifies the identity and security compliance of devices and users before granting network access, ensuring that only authorized entities can connect.
- Network Load Balancer (NLB): NLB distributes network traffic across multiple servers to optimize performance and availability while preventing overload or denial-of-service attacks.
- Web Filter: Web filters restrict access to malicious or inappropriate websites based on predefined policies, protecting users from potential threats and unauthorized content.
- Spam Filter: Spam filters identify and block unsolicited and malicious emails, reducing the risk of phishing attacks and malware distribution.
- Proxy Server: Proxy servers act as intermediaries between clients and servers, enhancing security by masking the client's identity and providing additional layers of protection.
- Virtual Private Networks (VPNs): VPNs create secure encrypted connections over public networks, allowing remote users to securely access private networks and data.
- VPN Gateways: VPN gateways enable secure encrypted connections over public networks, allowing remote users to access private networks and data securely.
- Network Access Control (NAC): NAC ensures that only authorized devices and users can access the network. It verifies the identity and security compliance of devices before granting network access.
- Network Segmentation: Network segmentation divides the network into separate segments or subnets, isolating critical resources and limiting the impact of potential security breaches.
- Secure Network Protocols: Secure protocols such as Transport Layer Security (TLS) and Secure Shell (SSH) encrypt network communications to protect data integrity and confidentiality.
- Email Security Gateways: Email security gateways scan incoming and outgoing emails, filtering out spam, malware, and malicious attachments to protect against email-based threats.
- Content Filtering Devices: Content filtering devices inspect network traffic and block access to unauthorized or inappropriate content, ensuring compliance with security policies.
- Network Device Backup and Recovery: Regularly backing up network device configurations and data helps ensure quick recovery in the event of a security incident or device failure.
- Security Monitoring and Logging: Network security involves continuous monitoring of network traffic, event logs, and security alerts to detect and respond to potential security incidents.
- Security Information and Event Management (SIEM): SIEM systems collect and analyze security event logs from various network devices, helping to detect and respond to security incidents effectively.
- Security Policies and User Awareness: Establishing and enforcing security policies and educating users about best practices and potential risks are essential aspects of network security.
By implementing these robust network security measures, organizations can effectively safeguard their networks, prevent unauthorized access, protect sensitive data, maintain business continuity, and earn the trust of users and stakeholders. Network security is a critical component and plays a vital role in an overall comprehensive cybersecurity strategy.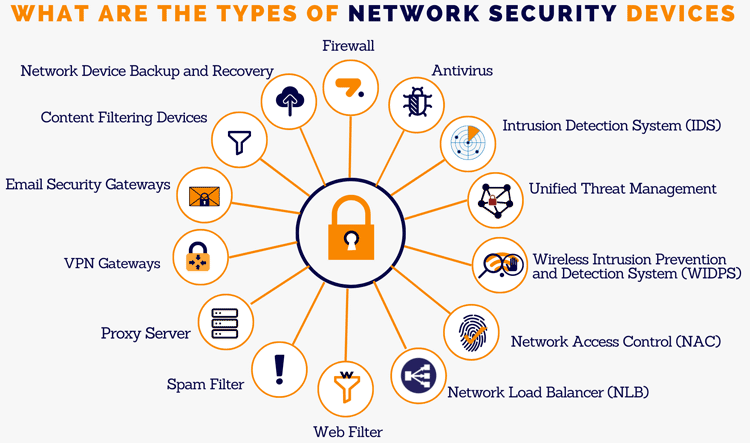
How does network security work?
Network security operates through a multi-layered approach, combining various defense mechanisms to safeguard the network against unauthorized access, threats, and exploits. These layers work together to enforce policies, controls, and encryption methods, allowing authorized users to access network resources while preventing malicious actors from compromising the network.
By deploying network security measures in a layered approach, organizations can establish a robust defense system that protects network resources, prevents unauthorized access, detects and mitigates threats, and ensures the confidentiality, integrity, and availability of data and network services. Network security is an ongoing process that requires regular updates, monitoring, and adaptation to counter evolving threats in today's interconnected world.
Authentication and authorization are two procedures that are important to network security.
Understanding Authentication and Authorization
Authentication is the crucial process of verifying the identity of users to ensure that they are who they claim to be. It serves as the initial stage in any security procedure, providing a safeguard against unauthorized intrusions into the network.
To authenticate users, various methods are commonly employed:
- Passwords: The most widely used authentication method involves usernames and passwords. When users input the correct credentials, the system assumes their identity is valid and grants access.
- Pins: These unique codes are used for a single session or transaction and are rendered invalid after use.
- Authentication Apps: These third-party applications generate security codes that allow access when entered correctly.
- Biometrics: Users must provide their fingerprint or undergo an eye scan to gain access to the system.
In certain cases, systems require the successful verification of multiple parameters. This practice, known as multi-factor authentication (MFA) or two-factor authentication (2FA), adds an extra layer of protection beyond passwords alone.
Authorization, on the other hand, focuses on granting individuals access to specific resources or functions within a system's security framework. Authorization, also referred to as access control or access privilege, determines the level of access granted to an authorized user. For example, a network administrator may require access to the entire network, while other individuals operating within it may only need access to specific portions. The process of establishing the appropriate access level or permission based on the user's role within the network is known as authorization.
How organizations benefit from network security?
Network security offers numerous benefits to both individuals and organizations in today's digital landscape. By implementing robust network security measures, organizations can experience the following advantages:
- Protection against Cyber Threats: Network security safeguards an organization's network infrastructure, devices, and data from various cyber threats, including malware, ransomware, phishing attacks, and data breaches. It acts as a shield to prevent unauthorized access and potential damage to sensitive information.
- Safeguarding Confidentiality and Privacy: Network security measures, such as encryption and secure protocols, ensure the confidentiality and privacy of an organization's data during transmission. This protection is particularly crucial for organizations that handle sensitive customer information, financial data, or proprietary information.
- Mitigating Financial Losses: Successful cyberattacks can result in significant financial losses, including data theft, business disruption, reputational damage, legal liabilities, and regulatory penalties. Network security reduces the risk of such incidents, helping organizations avoid costly consequences associated with cyber incidents.
- Maintaining Business Continuity: Network security measures enable organizations to maintain uninterrupted operations. By preventing unauthorized access, network disruptions, and malware infections, organizations can ensure the availability and reliability of their network services and systems, minimizing downtime and productivity losses.
- Safeguarding Customer Trust: Demonstrating a commitment to network security helps build trust with customers and stakeholders. When customers feel confident that their personal information is protected, they are more likely to engage with the organization, share sensitive data, and maintain a long-term relationship with the organization's brand.
- Compliance with Regulations: Many industries have specific regulatory requirements related to network security and data protection. By implementing network security measures, organizations can ensure compliance with applicable regulations, avoiding penalties and legal consequences.
- Protection against Reputation Damage: A security breach can significantly damage an organization's reputation. Network security helps prevent such incidents, safeguarding the organization's reputation and maintaining the trust of customers, partners, and employees.
- Enhanced Productivity and Efficiency: When an organization's network is secure, employees can work with peace of mind, knowing that their data and systems are protected. This promotes productivity and efficiency as employees can focus on their tasks without concerns about potential cyber threats.
- Prevention of Intellectual Property Theft: Network security measures protect proprietary information, trade secrets, and intellectual property from unauthorized access or theft. This is especially critical for organizations that rely on innovation and unique assets as part of their competitive advantage.
- Peace of Mind: Finally, network security provides peace of mind, knowing that the organization has taken necessary precautions to protect valuable assets. It allows the organization to focus on its core business objectives without constant worry about potential cyber threats.
By investing in network security, organizations can enjoy these benefits and create a secure environment for their organization, employees, and customers, ultimately safeguarding their reputation and supporting long-term success.
Network Security and Defense
- FortiGate is a brand of Next Generation Firewalls (NGFW) developed by Fortinet. FortiGate NGFWs are advanced security appliances designed to provide comprehensive network protection and threat management. They incorporate various security features and technologies to deliver enhanced visibility, control, and protection against evolving cyber threats. FortiGate NGFWs are widely used in organizations of all sizes, ranging from small businesses to large enterprises, across different industries. They provide a comprehensive security solution that combines multiple security functions into a single platform, reducing complexity and improving network protection against advanced threats. Key features and capabilities of FortiGate NGFW include:
- Deep Packet Inspection: FortiGate NGFWs perform deep packet inspection to analyze network traffic at the application layer. This enables the identification and prevention of advanced threats, including malware, viruses, and intrusion attempts.
- Intrusion Prevention System (IPS): FortiGate NGFWs include an IPS module that detects and blocks network attacks in real-time. It uses signatures, behavioral analysis, and anomaly detection to identify and stop malicious activities.
- Application Control: FortiGate NGFWs provide granular control over applications and can enforce policies based on specific applications or categories. This helps organizations manage bandwidth usage, prioritize critical applications, and prevent unauthorized application access.
- Web Filtering: FortiGate NGFWs can apply web filtering policies to restrict access to inappropriate or malicious websites. This helps enforce acceptable use policies and protects users from accessing potentially harmful content.
- Advanced Threat Protection: FortiGate NGFWs integrate advanced threat protection features such as sandboxing, antivirus scanning, and botnet detection. These capabilities help identify and mitigate zero-day threats and sophisticated malware.
- Virtual Private Network (VPN): FortiGate NGFWs support secure VPN connectivity, allowing remote users and branch offices to securely access the network resources. They provide encryption and authentication mechanisms to ensure data privacy and integrity.
- Centralized Management: FortiGate NGFWs can be managed through a central management console, enabling administrators to configure policies, monitor network activity, and receive real-time alerts. This simplifies security management across distributed networks.
- Scalability and Performance: FortiGate NGFWs are available in various models with different performance levels to accommodate the needs of different network sizes and traffic volumes. They are designed to scale and handle high network throughput without compromising security.
- Deep Packet Inspection: FortiGate NGFWs perform deep packet inspection to analyze network traffic at the application layer. This enables the identification and prevention of advanced threats, including malware, viruses, and intrusion attempts.
- Check Point Quantum is a term used to refer to Check Point's Security Gateway Next Generation Firewall. Check Point's Security Gateway Next Generation Firewall, often referred to as Quantum Security Gateway, is a comprehensive security solution that combines firewall functionality with advanced threat prevention capabilities. It is designed to protect networks and assets from various cyber threats, including malware, intrusions, and data breaches. The Check Point Quantum Security Gateway offers centralized management through Check Point's Security Management platform, allowing administrators to configure, monitor, and manage security policies across the network from a single console. Overall, Check Point Quantum Security Gateway is a robust and feature-rich next-generation firewall solution designed to protect organizations' networks from a wide range of cyber threats while offering advanced threat prevention capabilities. The Security Gateway Next Generation Firewall incorporates multiple security features and technologies to provide comprehensive protection. These may include:
- Firewall: It acts as a traditional firewall, controlling inbound and outbound traffic based on defined security policies and rules.
- Intrusion Prevention System (IPS): It inspects network traffic in real-time to detect and prevent network-based attacks and exploits.
- Application Control: It enables granular control over applications and protocols, allowing organizations to define and enforce policies regarding application usage.
- Antivirus and Anti-Malware: It scans network traffic and files for known malware signatures, preventing the spread of malicious software.
- Threat Emulation and Sandboxing: It executes suspicious files and URLs in a controlled environment to identify and prevent zero-day attacks and unknown threats.
- Data Loss Prevention (DLP): It monitors and controls sensitive data transfers, preventing unauthorized disclosure or leakage of sensitive information.
- VPN and Remote Access: It provides secure remote access capabilities, allowing authorized users to connect to the network securely from remote locations.
- Identity Awareness: It integrates with identity management systems to enforce user-based security policies and provide secure access control.
- Firewall: It acts as a traditional firewall, controlling inbound and outbound traffic based on defined security policies and rules.
- PA-Series refers to Palo Alto Networks' line of next-generation firewalls (NGFWs). Palo Alto Networks is a leading cybersecurity company that specializes in providing advanced security solutions for networks and enterprises. The PA-Series NGFWs are designed to provide comprehensive network security by combining traditional firewall functionality with advanced threat prevention capabilities. These firewalls offer a wide range of features and technologies to protect networks from various cyber threats, including malware, exploits, and unauthorized access. The PA-Series NGFWs are known for their high performance, scalability, and advanced security features. They are widely used in organizations of all sizes, including enterprises, government agencies, and service providers, to secure their networks and protect against evolving cyber threats. Key features of the PA-Series NGFWs may include:
- Firewall: The PA-Series NGFWs act as traditional firewalls, controlling and monitoring network traffic based on predefined security policies and rules.
- Intrusion Prevention System (IPS): They include built-in IPS capabilities to detect and prevent network-based attacks, including known vulnerabilities and exploits.
- Application Visibility and Control: These firewalls provide granular visibility into network applications and allow administrators to define policies for application usage, ensuring that only authorized applications are allowed.
- Advanced Threat Prevention: The PA-Series NGFWs employ advanced threat prevention techniques, such as malware analysis, sandboxing, and behavioral analysis, to detect and block unknown and zero-day threats.
- VPN and Remote Access: They offer secure remote access capabilities, allowing authorized users to connect to the network securely from remote locations using virtual private network (VPN) connections.
- URL Filtering: The NGFWs can inspect and filter web traffic based on predefined URL categories, providing protection against malicious websites and enforcing web usage policies.
- User-based Policies: They integrate with identity management systems to enforce security policies based on user identities, enabling granular access control and authentication.
- Centralized Management: The PA-Series NGFWs can be managed centrally through a management console, allowing administrators to configure, monitor, and update security policies across multiple devices from a single interface.
- Firewall: The PA-Series NGFWs act as traditional firewalls, controlling and monitoring network traffic based on predefined security policies and rules.
- Cisco Secure Firewall is a comprehensive network security solution provided by Cisco Systems, a leading networking and cybersecurity company. It is a next-generation firewall (NGFW) that combines traditional firewall functionality with advanced threat protection capabilities to secure networks and data. Cisco Secure Firewall is designed for scalability, high performance, and integration with other Cisco security products and solutions. It is widely used by organizations of all sizes, including enterprises, government agencies, and service providers, to protect their networks and critical assets from cyber threats. Cisco Secure Firewall offers a range of features and technologies to protect organizations from various cyber threats, including malware, intrusions, and unauthorized access. Some key features and capabilities of Cisco Secure Firewall include:
- Firewall Protection: It acts as a traditional firewall, controlling and monitoring network traffic based on predefined security policies and rules. It inspects packets at the network and application layers to enforce security policies and prevent unauthorized access.
- Intrusion Prevention System (IPS): Cisco Secure Firewall includes an integrated IPS that detects and prevents network-based attacks, including known vulnerabilities and exploits. It can identify and block malicious traffic and suspicious behavior patterns to protect against intrusion attempts.
- Advanced Threat Protection: It employs advanced threat detection and prevention mechanisms, such as malware detection, sandboxing, and behavioral analysis, to identify and block unknown and zero-day threats. Cisco's threat intelligence and machine learning capabilities enhance its ability to detect and respond to sophisticated attacks.
- Secure Remote Access: Cisco Secure Firewall provides secure remote access capabilities, allowing authorized users to connect to the network securely from remote locations using virtual private network (VPN) connections. It ensures encrypted and authenticated communication between remote users and the network.
- Application Visibility and Control: It offers granular visibility into network applications and allows administrators to define policies for application usage. This enables organizations to enforce access controls, prioritize critical applications, and detect and block unauthorized applications.
- Web Filtering: Cisco Secure Firewall includes web filtering capabilities to inspect and control web traffic. It can enforce URL filtering policies, block access to malicious or inappropriate websites, and prevent web-based threats.
- Network Segmentation: It supports network segmentation by creating virtual firewalls or security zones within the network. This allows organizations to enforce separate security policies and controls for different network segments, enhancing overall network security.
- Centralized Management: Cisco Secure Firewall can be centrally managed through Cisco's Security Management Center (formerly known as Firepower Management Center). It provides a centralized interface for configuration, monitoring, and reporting across multiple firewall instances, simplifying management and ensuring consistent security policies.
- Firewall Protection: It acts as a traditional firewall, controlling and monitoring network traffic based on predefined security policies and rules. It inspects packets at the network and application layers to enforce security policies and prevent unauthorized access.
- Sophos Firewall is a network security solution provided by Sophos, a leading cybersecurity company. It is a comprehensive next-generation firewall (NGFW) that combines traditional firewall capabilities with advanced security features to protect networks from various threats. Sophos Firewall is designed to be easy to deploy, use, and manage. It offers comprehensive security capabilities in a single appliance or virtual form factor, suitable for small to large organizations. Sophos also integrates its firewall with other security products, such as endpoint protection and cloud security, to provide a synchronized defense against evolving threats. Sophos Firewall offers a wide range of features and functionalities to secure networks and ensure effective threat prevention. Some key features of Sophos Firewall include:
- Firewall Protection: Sophos Firewall acts as a traditional firewall, controlling and monitoring network traffic based on predefined security policies. It inspects packets at the network and application layers to enforce access controls and prevent unauthorized access.
- Intrusion Prevention System (IPS): It includes an integrated IPS that detects and prevents network-based attacks, such as malware, exploits, and intrusion attempts. The IPS engine analyzes network traffic in real-time and blocks malicious activities.
- Advanced Threat Protection: Sophos Firewall employs advanced threat detection and prevention mechanisms, including signature-based detection, heuristic analysis, and machine learning algorithms. It can detect and block known and unknown threats, including zero-day attacks.
- Web Filtering: Sophos Firewall offers web filtering capabilities to control and monitor web traffic. It can enforce URL filtering policies, block access to malicious or inappropriate websites, and protect against web-based threats, including phishing and malware downloads.
- Application Control: It provides granular visibility and control over network applications. Administrators can define policies to allow or block specific applications based on their risk level or user requirements. This enables organizations to manage application usage and protect against unauthorized or risky applications.
- VPN Connectivity: Sophos Firewall supports secure remote access through virtual private network (VPN) connections. It enables remote users to securely connect to the network and access resources while ensuring encrypted and authenticated communication.
- Network Segmentation: It supports network segmentation by creating separate security zones or virtual firewalls within the network. This allows organizations to enforce different security policies for different network segments and restrict lateral movement of threats.
- Centralized Management: Sophos Firewall can be centrally managed through a unified management console, such as Sophos Central or Sophos XG Firewall Manager. This provides a single interface for configuration, monitoring, and reporting across multiple firewall instances, simplifying management and ensuring consistent security policies.
- Firewall Protection: Sophos Firewall acts as a traditional firewall, controlling and monitoring network traffic based on predefined security policies. It inspects packets at the network and application layers to enforce access controls and prevent unauthorized access.
- Cisco Meraki MX appliances are security and networking devices that are part of the Cisco Meraki cloud-managed networking solution. These appliances combine security features, such as firewall, VPN, and intrusion prevention, with networking functionalities, including routing and switching, in a single integrated device. The Cisco Meraki MX appliances are designed to provide comprehensive security and networking capabilities in a cloud-managed solution. They are suitable for small to large organizations, including distributed branch offices and remote sites, offering simplified management, enhanced security, and optimized network connectivity. Key features and capabilities of Cisco Meraki MX appliances include:
- Cloud-Managed: Cisco Meraki MX appliances are centrally managed through the cloud-based Meraki Dashboard. This allows administrators to easily deploy, configure, and monitor multiple MX devices from a single web-based interface, regardless of their physical location.
- Firewall and Security: The MX appliances provide stateful firewall capabilities to enforce access control policies and protect networks from unauthorized access. They offer advanced security features, such as Intrusion Detection and Prevention System (IDPS), content filtering, web search filtering, and anti-malware protection.
- VPN Connectivity: The MX appliances support secure site-to-site VPN connectivity, allowing organizations to establish encrypted connections between different locations. Remote users can also use client VPN to securely access the network from anywhere.
- SD-WAN Capabilities: Cisco Meraki MX appliances incorporate Software-Defined Wide Area Networking (SD-WAN) capabilities, enabling organizations to optimize and prioritize network traffic across multiple sites. This ensures efficient utilization of available bandwidth and improved application performance.
- Networking Features: MX appliances function as routers and switches, providing routing, VLAN support, DHCP services, Quality of Service (QoS) settings, and more. They integrate seamlessly with other Cisco Meraki devices, such as access points and switches, to create a unified and scalable network infrastructure.
- Auto VPN: The Auto VPN feature simplifies the process of establishing VPN tunnels between Meraki MX appliances, eliminating the need for complex manual configurations. It enables secure connectivity between branch offices or remote sites with minimal effort.
- Unified Threat Management (UTM): Cisco Meraki MX appliances offer UTM capabilities by combining various security features into a single device. This includes firewall, anti-malware, web filtering, and intrusion prevention. UTM simplifies security management and reduces the need for multiple standalone security appliances.
- Analytics and Reporting: The Meraki Dashboard provides real-time visibility into network traffic, security events, and client devices. Administrators can access detailed analytics, generate reports, and gain insights into network performance and security posture.
- Cloud-Managed: Cisco Meraki MX appliances are centrally managed through the cloud-based Meraki Dashboard. This allows administrators to easily deploy, configure, and monitor multiple MX devices from a single web-based interface, regardless of their physical location.
- Firebox refers to the line of network security appliances developed by WatchGuard Technologies. These appliances, known as WatchGuard Fireboxes, provide firewall and security services to protect networks from various threats and intrusions. Firebox appliances are designed to deliver robust security capabilities, protect networks from cyber threats, and provide secure connectivity for organizations of all sizes. They offer a comprehensive set of features to help maintain network integrity, confidentiality, and availability, making them suitable for a wide range of industries and network environments. Key features and capabilities of Firebox appliances include:
- Firewall Protection: Firebox appliances function as stateful inspection firewalls, monitoring incoming and outgoing network traffic and enforcing access control policies. They examine packet-level information to determine whether to allow or block traffic based on predefined rules.
- Unified Threat Management (UTM): Firebox appliances offer a range of security services integrated into a single device, providing comprehensive protection against various threats. These services may include antivirus and anti-malware scanning, intrusion prevention, spam blocking, web filtering, and data loss prevention.
- VPN Connectivity: Firebox appliances support secure virtual private network (VPN) connectivity, allowing remote users or branch offices to securely access the network over encrypted tunnels. This enables secure communication and remote access to resources while maintaining data privacy.
- Traffic Management and QoS: Fireboxes provide capabilities for traffic shaping and Quality of Service (QoS) management. Administrators can prioritize network traffic based on application type or specific requirements, ensuring optimal performance for critical applications.
- Centralized Management: WatchGuard offers a central management platform called WatchGuard System Manager (WSM) to configure, monitor, and manage Firebox appliances across the network. This simplifies administration and provides centralized control over security policies and configurations.
- Reporting and Logging: Firebox appliances generate detailed logs and reports on network activity, security events, and system health. Administrators can analyze these logs to gain insights into network threats, identify security vulnerabilities, and track user activity.
- High Availability and Redundancy: To ensure uninterrupted network security, Firebox appliances can be deployed in high availability configurations. Redundant units are set up to operate in an active-passive mode, automatically taking over if a primary appliance fails.
- Scalability and Flexibility: Firebox appliances are available in various models to accommodate different network sizes and performance requirements. They can be deployed as standalone units or in a distributed architecture to protect multiple sites or branch offices.
- Firewall Protection: Firebox appliances function as stateful inspection firewalls, monitoring incoming and outgoing network traffic and enforcing access control policies. They examine packet-level information to determine whether to allow or block traffic based on predefined rules.
- SRX Series refers to a line of network security devices developed by Juniper Networks. These devices are known as Juniper SRX Series Services Gateways and are designed to provide advanced security and networking capabilities for various network environments, from small businesses to large enterprises and service providers. The SRX Series is known for its scalability, flexibility, and high-performance capabilities. It offers a comprehensive set of security features to protect networks from advanced threats, provide secure connectivity, and enable efficient network management. The devices are widely used in various industries and network environments, including data centers, branch offices, and service provider networks. Key features and capabilities of the SRX Series include:
- Next-Generation Firewall: The SRX Series devices offer next-generation firewall capabilities, combining traditional firewall functionality with advanced security features. They can perform deep packet inspection, application-level control, and threat intelligence to protect networks against a wide range of threats.
- Intrusion Prevention System (IPS): SRX Series devices incorporate an IPS to detect and prevent network intrusions. They analyze network traffic in real-time, looking for known attack signatures and anomalous behavior to identify and block potential threats.
- VPN and Secure Connectivity: The SRX Series supports virtual private network (VPN) connectivity, allowing secure remote access to the network for users working remotely or connecting from branch offices. It offers various VPN protocols and encryption options to ensure secure communication and data privacy.
- Unified Threat Management (UTM): Some models within the SRX Series provide unified threat management features, including antivirus, anti-malware, web filtering, and content filtering capabilities. This consolidated approach simplifies security management and provides comprehensive protection against multiple types of threats.
- Advanced Routing and Networking: The SRX Series devices include robust routing capabilities, supporting dynamic routing protocols and enabling secure connectivity between different network segments. They can handle complex network topologies and provide high-performance routing functionality.
- Network Segmentation: With virtualization capabilities, the SRX Series allows network segmentation by creating logical networks and enforcing security policies between them. This enhances network security by isolating different network segments and preventing lateral movement of threats.
- Centralized Management: Juniper Networks provides Junos Space Security Director, a centralized management platform for configuring, monitoring, and managing SRX Series devices. It offers a single pane of glass for security policy management, threat visibility, and security event monitoring.
- High Availability and Redundancy: The SRX Series supports high availability configurations to ensure continuous network security. Redundant units can be deployed in active-passive mode, automatically taking over if a primary device fails, minimizing downtime and maintaining business continuity.
- Next-Generation Firewall: The SRX Series devices offer next-generation firewall capabilities, combining traditional firewall functionality with advanced security features. They can perform deep packet inspection, application-level control, and threat intelligence to protect networks against a wide range of threats.
- Barracuda CloudGen Firewall is a network security solution developed by Barracuda Networks. It is designed to provide advanced security, connectivity, and control for networks of all sizes, from small businesses to large enterprises. The CloudGen Firewall combines traditional firewall capabilities with additional features to deliver comprehensive network protection and optimize network performance. Barracuda CloudGen Firewall is available in various form factors, including physical appliances, virtual appliances, and cloud-based deployments. This flexibility allows organizations to choose the deployment model that best suits their needs, whether it's on-premises, in virtualized environments, or in the cloud. Overall, the Barracuda CloudGen Firewall offers comprehensive security features, advanced threat protection, and network optimization capabilities, making it a robust solution for protecting networks and ensuring secure connectivity in today's evolving threat landscape. Key features and capabilities of the Barracuda CloudGen Firewall include:
- Next-Generation Firewall (NGFW): The CloudGen Firewall incorporates next-generation firewall capabilities, allowing for granular control over network traffic at the application level. It can enforce security policies based on application, user, and content, providing enhanced protection against evolving threats.
- Intrusion Detection and Prevention System (IDPS): The CloudGen Firewall includes an IDPS that monitors network traffic for suspicious behavior and potential threats. It can detect and prevent various types of attacks, such as malware infections, network intrusions, and denial-of-service (DoS) attacks.
- Secure Remote Access: The CloudGen Firewall enables secure remote access to the network through virtual private network (VPN) connections. It supports various VPN protocols, including SSL VPN and IPsec VPN, ensuring encrypted and authenticated communication for remote users and branch offices.
- Web Filtering and Application Control: It offers web filtering capabilities to control and monitor web traffic, blocking access to malicious or inappropriate websites. Additionally, application control features allow administrators to define policies for specific applications, controlling their usage and ensuring compliance.
- Advanced Threat Protection: The CloudGen Firewall incorporates advanced threat protection mechanisms, such as antivirus scanning, anti-malware detection, and sandboxing. These features help identify and block threats, including viruses, ransomware, and zero-day attacks.
- Traffic Optimization and QoS: It includes traffic optimization features that prioritize network traffic and allocate bandwidth based on predefined policies. Quality of Service (QoS) capabilities allow administrators to control and manage bandwidth usage, ensuring optimal performance for critical applications and services.
- Centralized Management: Barracuda CloudGen Firewall can be centrally managed through Barracuda Cloud Control, a web-based management console. It provides a single interface for configuration, monitoring, and reporting across multiple CloudGen Firewall deployments, simplifying network management and enhancing visibility.
- High Availability and Redundancy: The CloudGen Firewall supports high availability configurations to ensure uninterrupted network security. Redundant units can be deployed in active-passive or active-active mode, providing failover protection and minimizing downtime.
- Next-Generation Firewall (NGFW): The CloudGen Firewall incorporates next-generation firewall capabilities, allowing for granular control over network traffic at the application level. It can enforce security policies based on application, user, and content, providing enhanced protection against evolving threats.
- SonicWall NSA (Network Security Appliance) Series is a line of next-generation firewalls (NGFWs) developed by SonicWall, a cybersecurity company. The NSA Series is designed to provide advanced network security, threat prevention, and secure remote access capabilities for businesses of all sizes, from small offices to large enterprises. The SonicWall NSA Series offers a range of models with varying performance levels and features to cater to different network sizes and requirements. Whether deployed as hardware appliances, virtual appliances, or in the cloud, the NSA Series aims to deliver comprehensive network security, threat prevention, and secure connectivity for businesses seeking robust protection against evolving cyber threats. Key features and capabilities of the SonicWall NSA Series include:
- Next-Generation Firewall (NGFW): The NSA Series incorporates next-generation firewall technology, enabling deep packet inspection and granular control over network traffic. It can enforce security policies based on application, user, and content, providing enhanced protection against advanced threats and malware.
- Intrusion Prevention System (IPS): The NSA Series includes an IPS that monitors network traffic in real-time, detecting and preventing network-based attacks. It uses signature-based and behavior-based detection techniques to identify and block malicious activities, helping to protect networks from various threats.
- Secure Remote Access: It offers secure remote access capabilities through Virtual Private Network (VPN) connections. The NSA Series supports multiple VPN protocols, including SSL VPN and IPsec VPN, allowing remote users and branch offices to securely connect to the corporate network.
- Advanced Threat Protection: The NSA Series incorporates advanced threat protection mechanisms, such as anti-malware scanning, cloud-based sandboxing, and real-time threat intelligence feeds. These features help detect and block advanced threats, including zero-day attacks, ransomware, and botnets.
- Content Filtering: It includes web content filtering capabilities that allow administrators to control and monitor web browsing activities. The NSA Series can block access to malicious or inappropriate websites, enforce acceptable use policies, and provide detailed reporting on web usage.
- Application Control: The NSA Series enables administrators to control and manage application usage on the network. It offers granular application-level control, allowing policies to be defined based on specific applications, categories, or application characteristics. This helps organizations ensure productivity, security, and compliance.
- High Availability and Scalability: The NSA Series supports high availability configurations for redundancy and failover protection. It can be deployed in active-passive or active-active modes to ensure uninterrupted network security. Additionally, the series is scalable, allowing organizations to expand their security capabilities as their network requirements grow.
- Centralized Management: SonicWall provides a centralized management platform called SonicWall GMS (Global Management System) for managing and monitoring multiple NSA appliances from a single interface. It allows administrators to streamline policy deployment, generate reports, and gain visibility into network security across distributed environments.
- Next-Generation Firewall (NGFW): The NSA Series incorporates next-generation firewall technology, enabling deep packet inspection and granular control over network traffic. It can enforce security policies based on application, user, and content, providing enhanced protection against advanced threats and malware.
- Cisco ASA (Adaptive Security Appliance) Firewall is a security device provided by Cisco Systems. It is a next-generation firewall that offers advanced security features and capabilities to protect networks and resources from various threats. Cisco ASA Firewall is a widely deployed security solution known for its robustness, reliability, and extensive feature set. It provides organizations with a comprehensive security framework to safeguard their networks, applications, and data from various threats, helping to ensure a secure and resilient IT environment. Key features and capabilities of Cisco ASA Firewall include:
- Firewall Functionality: Cisco ASA Firewall serves as a traditional stateful inspection firewall, providing packet filtering and access control capabilities. It monitors and controls incoming and outgoing network traffic based on predefined security policies, allowing or denying traffic based on factors such as source/destination IP addresses, ports, and protocols.
- VPN (Virtual Private Network) Support: Cisco ASA Firewall offers built-in VPN functionality, allowing secure remote access to corporate networks and enabling secure communication between multiple locations. It supports various VPN protocols, including IPsec (Internet Protocol Security) and SSL/TLS (Secure Sockets Layer/Transport Layer Security), providing encrypted and authenticated connections for remote users and site-to-site connectivity.
- Intrusion Prevention System (IPS): Cisco ASA Firewall incorporates an intrusion prevention system that helps detect and prevent network intrusions and malicious activities. It utilizes a combination of signature-based and behavior-based techniques to identify and block potential threats, providing an additional layer of defense against attacks.
- Advanced Threat Detection: Cisco ASA Firewall includes advanced threat detection capabilities, such as malware and botnet detection. It leverages threat intelligence feeds and sophisticated algorithms to identify and block known and emerging threats, providing enhanced protection against malware, ransomware, and other malicious activities.
- Application Visibility and Control: Cisco ASA Firewall offers application-layer visibility and control, allowing administrators to identify and control specific applications and their usage within the network. This helps in enforcing policies related to application access, bandwidth allocation, and prioritization, enhancing network performance and security.
- High Availability and Scalability: Cisco ASA Firewall supports high availability configurations, allowing for redundant deployments to ensure continuous operation and minimal downtime. It also offers scalability options to accommodate growing network requirements, allowing organizations to expand their firewall capabilities as their needs evolve.
- Management and Monitoring: Cisco ASA Firewall can be centrally managed and monitored using Cisco Security Manager or Cisco Firepower Management Center. These management platforms provide a unified view of security policies, traffic analysis, logging, and reporting, making it easier for administrators to configure, monitor, and maintain the firewall.
- Integration with Cisco Security Ecosystem: Cisco ASA Firewall integrates with other Cisco security solutions and services, such as Cisco Advanced Malware Protection (AMP), Cisco Umbrella (DNS-layer security), and Cisco Threat Intelligence Director (threat intelligence aggregation and sharing). This integration enhances the overall security posture and effectiveness of the network infrastructure.
- Firewall Functionality: Cisco ASA Firewall serves as a traditional stateful inspection firewall, providing packet filtering and access control capabilities. It monitors and controls incoming and outgoing network traffic based on predefined security policies, allowing or denying traffic based on factors such as source/destination IP addresses, ports, and protocols.
- Azure Firewall is a cloud-based network security service provided by Microsoft Azure, the cloud computing platform by Microsoft. It serves as a highly scalable and fully managed firewall solution for securing virtual networks and resources within the Azure environment. Azure Firewall provides a secure and scalable firewall solution for organizations leveraging Azure cloud services. By deploying Azure Firewall, businesses can enforce network security policies, control access to resources, and protect their applications and data from unauthorized access or threats within the Azure environment. Key features and capabilities of Azure Firewall include:
- Network Traffic Filtering: Azure Firewall acts as a network traffic filter, allowing organizations to define and enforce network access policies. It operates at both the application and network layers, providing granular control over inbound and outbound traffic based on source/destination IP addresses, ports, and protocols.
- Application Focused: Azure Firewall is application-focused and understands specific protocols, such as HTTP, HTTPS, and SQL. It allows organizations to create application-specific rules to allow or deny access to applications based on their characteristics, helping protect against application-level threats.
- Threat Intelligence Integration: Azure Firewall integrates with Azure Threat Intelligence, leveraging Microsoft's vast threat intelligence network. This integration enables the firewall to dynamically block traffic from known malicious IP addresses and domains, enhancing security against emerging threats.
- High Availability: Azure Firewall supports high availability configurations with built-in auto-scaling capabilities. It can be deployed in an active-standby mode across multiple Azure regions to ensure continuous availability and resiliency.
- Integration with Azure Services: Azure Firewall seamlessly integrates with other Azure services, such as Azure Virtual Network (VNet), Azure Monitor, Azure Log Analytics, and Azure Active Directory (AD). This integration allows for better visibility, monitoring, and centralized management of security policies.
- Centralized Management: Azure Firewall can be centrally managed using Azure Portal, Azure PowerShell, Azure CLI, or Azure Resource Manager (ARM) templates. It provides a unified view of network traffic, rule configuration, and monitoring, making it easier for administrators to manage and maintain security policies.
- Logging and Reporting: Azure Firewall offers extensive logging and reporting capabilities. It can log network traffic, including allowed and denied connections, and export logs to Azure Monitor or Azure Storage for analysis and auditing purposes. This helps organizations meet compliance requirements and gain insights into network traffic patterns.
- Integration with Azure Security Center: Azure Firewall integrates with Azure Security Center, a unified security management and monitoring platform. This integration enables security administrators to gain actionable insights, detect and respond to security threats, and ensure compliance across their Azure infrastructure.
- Network Traffic Filtering: Azure Firewall acts as a network traffic filter, allowing organizations to define and enforce network access policies. It operates at both the application and network layers, providing granular control over inbound and outbound traffic based on source/destination IP addresses, ports, and protocols.
- Suricata is a free and open-source network intrusion detection and prevention system (IDS/IPS) that provides real-time monitoring and analysis of network traffic to detect and prevent security threats and attacks. Overall, Suricata is a powerful and versatile network security tool that offers effective network security monitoring, threat detection, and prevention, scalability, customization, and integration capabilities, making it a valuable asset in defending against network-based attacks and securing critical systems and data. Here are some key benefits of Suricata:
- Effective threat detection: Suricata utilizes signature-based detection, anomaly-based detection, and behavioral analysis techniques to identify a wide range of security threats, including malware, exploits, intrusion attempts, and suspicious network activities. It helps organizations detect and respond to threats in real-time.
- High-performance and scalability: Suricata is designed to handle high-speed network traffic and is optimized for multi-threading and parallel processing. It can efficiently process large volumes of network data, making it suitable for high-bandwidth environments and systems with multiple cores or processors.
- Customizable rule sets: Suricata supports its own rule language, allowing users to create custom rules or utilize existing rule sets to define the behavior and characteristics of network traffic that should be monitored. This flexibility enables organizations to tailor the detection capabilities of Suricata to their specific security requirements.
- Multi-protocol support: Suricata supports a wide range of network protocols, including TCP, UDP, HTTP, DNS, TLS, and more. This versatility allows it to monitor and analyze various types of network traffic across different protocols, making it suitable for diverse network environments.
- Open-source and active community: Suricata is an open-source project with an active and dedicated community of developers and users. This ensures regular updates, bug fixes, and the addition of new features to keep up with the evolving threat landscape and provide effective security measures.
- Integration with security ecosystems: Suricata can be integrated into existing security architectures and tools, such as SIEM (Security Information and Event Management) systems, threat intelligence platforms, and log management systems. This allows for centralized monitoring, correlation of security events, and streamlined incident response.
- Cost-effective solution: Being open-source, Suricata eliminates the need for expensive licensing fees associated with commercial IDS/IPS solutions. It provides a cost-effective way for organizations to enhance their network security posture without compromising on the quality and effectiveness of threat detection and prevention.
- Effective threat detection: Suricata utilizes signature-based detection, anomaly-based detection, and behavioral analysis techniques to identify a wide range of security threats, including malware, exploits, intrusion attempts, and suspicious network activities. It helps organizations detect and respond to threats in real-time.
Endpoint Protection
- VMware Carbon Black is a comprehensive endpoint security platform designed to protect organizations against advanced cyber threats. It combines multiple security capabilities, including antivirus, endpoint detection and response (EDR), next-generation antivirus (NGAV), and threat hunting, into a single solution. The platform leverages advanced technologies such as behavioral analysis, machine learning, and cloud-based threat intelligence to provide proactive and real-time protection against a wide range of threats, including malware, ransomware, fileless attacks, and other sophisticated threats. VMware Carbon Black focuses on endpoint visibility and detection, allowing security teams to monitor and analyze endpoint activities and behaviors in real-time. It provides detailed information about processes, network connections, file modifications, and other endpoint events, enabling organizations to quickly identify and respond to potential threats.
With its cloud-native architecture, VMware Carbon Black offers scalability, flexibility, and ease of deployment across distributed environments, including physical endpoints, virtual machines, cloud workloads, and remote workers. It enables organizations to protect their endpoints regardless of location, while also providing centralized management and visibility through a unified console. Overall, VMware Carbon Black is designed to help organizations strengthen their endpoint security, improve threat detection and response capabilities, and enhance their overall cybersecurity posture in an increasingly complex threat landscape. Key features of VMware Carbon Black include:
- Endpoint Protection: Provides advanced threat prevention, malware detection, and antivirus capabilities to protect endpoints from known and unknown threats.
- Endpoint Detection and Response (EDR): Offers real-time visibility into endpoint activities, behavioral analysis, threat hunting, and incident response capabilities to detect and respond to advanced threats.
- Cloud-Based Threat Intelligence: Leverages a global threat intelligence network to provide up-to-date information about emerging threats and deliver proactive protection.
- Threat Hunting: Enables security teams to proactively search for and investigate potential threats, leveraging advanced analytics and behavioral indicators to identify malicious activities.
- Security Analytics and Reporting: Provides comprehensive reporting and analytics to gain insights into security incidents, endpoint health, and overall security posture.
- Integration and Automation: Supports integration with other security solutions and tools, allowing organizations to build a unified security ecosystem and automate security workflows.
- Endpoint Protection: Provides advanced threat prevention, malware detection, and antivirus capabilities to protect endpoints from known and unknown threats.
- Sophos Intercept X Endpoint is an advanced endpoint protection solution designed to defend against sophisticated cyber threats and provide comprehensive security for endpoints within organizations. It combines a range of security technologies to deliver proactive, layered defense against malware, ransomware, exploits, and other advanced threats. Sophos Intercept X Endpoint is designed to provide comprehensive endpoint protection while minimizing the impact on system performance. It helps organizations stay ahead of emerging threats, detect and respond to incidents quickly, and reduce the risk of successful cyber attacks. Key features and capabilities of Sophos Intercept X Endpoint include:
- Next-Generation Anti-Malware: Utilizes advanced machine learning algorithms and behavioral analysis to detect and block known and unknown malware threats in real-time. It can identify malicious behavior patterns and stop attacks before they can execute.
- Exploit Prevention: Guards against exploit techniques used by attackers to compromise systems. Intercept X Endpoint proactively detects and blocks exploits, including zero-day attacks and fileless attacks, which target vulnerabilities in applications or operating systems.
- Ransomware Protection: Incorporates powerful anti-ransomware technology to stop ransomware attacks in their tracks. It can detect ransomware behavior, halt encryption processes, and rollback any changes made by ransomware to ensure data integrity.
- Endpoint Detection and Response (EDR): Offers comprehensive visibility into endpoint activities, allowing security teams to investigate and respond to security incidents. It provides detailed forensic data, enabling organizations to understand the scope and impact of an attack and take appropriate remediation actions.
- Root Cause Analysis: Provides insights into the root causes of incidents and offers actionable recommendations to strengthen security and prevent future attacks. It helps organizations identify vulnerabilities and address them effectively.
- Deep Learning Neural Networks: Leverages deep learning technology to identify and block both known and unknown malware threats. It can recognize malicious behaviors and patterns, even if the malware has not been seen before.
- Centralized Management: Offers a centralized console for simplified management and control of endpoint security across the organization. Security policies can be easily configured, deployed, and enforced from a single interface.
- Integration and Automation: Supports integration with other security solutions and allows for automated threat response workflows. It enables organizations to build a cohesive security ecosystem and streamline incident response processes.
- Next-Generation Anti-Malware: Utilizes advanced machine learning algorithms and behavioral analysis to detect and block known and unknown malware threats in real-time. It can identify malicious behavior patterns and stop attacks before they can execute.
- Trellix Endpoint Security, formerly known as McAfee Enterprise, is a comprehensive and centrally managed endpoint protection platform that offers advanced threat protection. With its advanced detection capabilities, including machine learning and credential theft monitoring, Trellix excels in threat detection. It also incorporates extended detection and response (XDR) capabilities. One of the key strengths of the Trellix platform is its robust threat detection and response, which seamlessly integrates with Windows environments. Through the use of machine learning and behavioral analysis, Trellix enables faster communication and threat detection among endpoints. This automation significantly reduces the need for manual detections and remediations, as Trellix provides automatic analysis, containment, and remediation of threats across your entire fleet of endpoints. Trellix Endpoint Security is particularly well-suited for larger organizations seeking a powerful and automated solution for endpoint security. Its emphasis on threat detection and response makes it an ideal choice. Moreover, the platform offers integration with XDR and MDR capabilities, enabling continuous threat monitoring and automated response. With Trellix, organizations can benefit from robust device-level protection alongside an integrated solution for endpoint protection. Key benefits of Trellix Endpoint Security:
- Comprehensive Endpoint Protection: Trellix Endpoint Security offers a robust set of security features to protect endpoints against a wide range of threats, including malware, ransomware, and other advanced attacks. It helps safeguard sensitive data and prevents unauthorized access to critical systems.
- Advanced Threat Detection: The solution utilizes advanced detection capabilities, such as machine learning algorithms, to identify and mitigate emerging threats. This proactive approach helps detect and block malicious activities before they can cause harm, providing stronger security defenses.
- Credential Theft Monitoring: Trellix Endpoint Security includes credential theft monitoring, which helps prevent unauthorized access to sensitive information by detecting and alerting on attempts to steal user credentials. This feature enhances overall security and reduces the risk of data breaches.
- Integrated Threat Intelligence: Trellix Endpoint Security leverages its global threat intelligence network to provide up-to-date information and insights into the latest threats and attack vectors. This intelligence helps organizations stay informed and adapt their security strategies to address evolving threats effectively.
- Extended Detection and Response (XDR): With its XDR capabilities, Trellix Endpoint Security enables organizations to correlate and analyze security data from multiple sources, including endpoints, networks, and the cloud. This holistic approach provides a comprehensive view of the threat landscape and facilitates faster threat detection, investigation, and response.
- Centralized Management and Visibility: The solution offers a centralized management console, allowing organizations to efficiently manage and monitor the security of their endpoints from a single interface. This streamlines security administration, improves operational efficiency, and provides centralized visibility into endpoint security posture.
- Simplified Security Administration: Trellix Endpoint Security simplifies security administration by providing a unified platform for managing endpoint protection. It enables organizations to streamline security workflows, deploy security policies across endpoints, and automate routine tasks, reducing the complexity of managing endpoint security.
- Scalability and Flexibility: The solution is designed to scale and adapt to the changing needs of organizations. It can accommodate varying deployment sizes, from small businesses to large enterprises, and supports diverse endpoint environments, including desktops, laptops, and servers.
- Comprehensive Endpoint Protection: Trellix Endpoint Security offers a robust set of security features to protect endpoints against a wide range of threats, including malware, ransomware, and other advanced attacks. It helps safeguard sensitive data and prevents unauthorized access to critical systems.
- Symantec Endpoint Security, now known as Broadcom Endpoint Security, is a comprehensive cybersecurity solution designed to protect endpoints (such as desktops, laptops, servers, and mobile devices) from various threats. It combines multiple security technologies and features into a single solution to provide robust endpoint protection. Symantec Endpoint Security is suitable for businesses of all sizes and provides a multi-layered defense approach to protect endpoints from a wide range of security risks. It aims to provide proactive threat prevention, effective detection, and efficient incident response to safeguard the organization's endpoints and sensitive data. Key features and capabilities of Symantec Endpoint Security include:
- Antivirus and Antispyware: Provides real-time protection against known and emerging malware threats, including viruses, worms, Trojans, spyware, and adware.
- Firewall: Monitors network traffic and controls incoming and outgoing connections to protect against unauthorized access and network-based attacks.
- Intrusion Prevention System (IPS): Detects and blocks network attacks and vulnerabilities, protecting endpoints from exploits and zero-day threats.
- Behavioral Analysis: Utilizes advanced machine learning and artificial intelligence techniques to identify and block suspicious behavior and potential threats.
- Application Control: Allows administrators to control which applications can run on endpoints, preventing the execution of unauthorized or malicious software.
- Device Control: Enables granular control over peripheral devices (such as USB drives) to prevent data leakage and protect against the introduction of malware through removable media.
- Web Protection: Blocks access to malicious websites, prevents phishing attacks, and filters web content to enforce acceptable use policies and enhance browsing security.
- Data Loss Prevention (DLP): Helps prevent sensitive data from being leaked or exfiltrated by monitoring and controlling data transfers and enforcing encryption and data protection policies.
- Endpoint Detection and Response (EDR): Provides advanced threat hunting, investigation, and incident response capabilities to detect and respond to sophisticated threats and targeted attacks.
- Centralized Management: Offers a centralized console for managing and monitoring endpoint security across the organization, allowing administrators to deploy policies, monitor security events, and generate reports.
- Antivirus and Antispyware: Provides real-time protection against known and emerging malware threats, including viruses, worms, Trojans, spyware, and adware.
- Trend Micro Apex One is an advanced endpoint security solution designed to protect endpoints, servers, and mobile devices within organizations. It provides comprehensive threat protection, data security, and centralized management capabilities to defend against a wide range of cyber threats. Trend Micro Apex One is suitable for businesses of all sizes, including enterprises and SMBs. It aims to provide comprehensive and proactive endpoint security to defend against evolving threats and protect sensitive data across the organization's endpoints and servers. Key features and capabilities of Trend Micro Apex One include:
- Threat Protection: Offers real-time protection against known and unknown malware, ransomware, viruses, and other malicious threats. It utilizes advanced machine learning and behavioral analysis techniques to detect and block emerging threats.
- Web and Email Security: Provides web filtering capabilities to block access to malicious websites and prevent users from visiting risky or inappropriate web content. It also includes email scanning and protection to detect and block email-based threats, such as phishing and spam.
- Endpoint Detection and Response (EDR): Offers advanced detection and response capabilities, allowing security teams to proactively hunt for threats, investigate security incidents, and conduct forensic analysis on endpoints.
- Vulnerability Management: Identifies and manages vulnerabilities in endpoints and applications, helping organizations prioritize and address security weaknesses to reduce the risk of exploitation.
- Data Loss Prevention (DLP): Monitors and protects sensitive data by enforcing policies and preventing unauthorized data transfers or leaks. It includes features such as data encryption, device control, and content-aware protection.
- Behavior Monitoring: Monitors endpoint behavior in real-time to detect and block suspicious activities and potential threats. It can identify malicious processes, file modifications, and unusual network traffic patterns.
- Centralized Management: Provides a centralized console for managing and monitoring endpoint security across the organization. It allows administrators to deploy security policies, conduct threat investigations, generate reports, and automate security tasks.
- Mobile Device Security: Extends security capabilities to mobile devices, enabling organizations to enforce security policies, detect mobile threats, and remotely manage devices.
- Integration and Automation: Integrates with other security solutions and third-party tools to enhance overall security posture. It also offers automation capabilities to streamline security operations and response.
- Threat Protection: Offers real-time protection against known and unknown malware, ransomware, viruses, and other malicious threats. It utilizes advanced machine learning and behavioral analysis techniques to detect and block emerging threats.
- CrowdStrike Falcon is a cloud-native endpoint protection platform (EPP) and endpoint detection and response (EDR) solution offered by CrowdStrike, a leading cybersecurity company. It provides advanced threat prevention, detection, and response capabilities to protect endpoints and workloads from cyber threats. CrowdStrike Falcon is designed to protect endpoints across various operating systems, including Windows, macOS, and Linux. Its cloud-native architecture enables scalability, easy deployment, and automatic updates, ensuring that organizations can stay protected against emerging threats. Key features and capabilities of CrowdStrike Falcon include:
- Next-Generation Antivirus (NGAV): CrowdStrike Falcon leverages artificial intelligence (AI) and machine learning (ML) algorithms to provide superior antivirus protection. It uses behavioral analysis and machine learning models to detect and block malware, ransomware, and other malicious files in real-time.
- Endpoint Detection and Response (EDR): CrowdStrike Falcon's EDR capabilities allow security teams to detect and investigate advanced threats and security incidents. It provides detailed visibility into endpoint activities, tracks indicators of compromise (IOCs), and enables incident response and threat hunting.
- Threat Intelligence: CrowdStrike Falcon incorporates global threat intelligence to stay up-to-date with the latest threat trends and tactics used by cyber attackers. This helps in proactively identifying and blocking known and unknown threats.
- Real-time Endpoint Protection: Falcon's cloud-native architecture allows for instant and continuous protection across all endpoints, regardless of their location. It provides real-time prevention, detection, and response capabilities to stop attacks before they can cause significant damage.
- Endpoint Vulnerability Management: The platform includes vulnerability management features to identify and remediate security vulnerabilities in the endpoints. It helps organizations prioritize and patch vulnerabilities to reduce the risk of exploitation.
- Incident Response and Forensics: CrowdStrike Falcon offers comprehensive incident response capabilities, allowing security teams to contain and mitigate threats quickly. It provides detailed forensics data and allows for remote investigation of endpoints to understand the scope and impact of an incident.
- Threat Hunting: CrowdStrike Falcon enables proactive threat hunting by allowing security analysts to search for signs of compromise and perform in-depth investigations across endpoints. It provides a range of search and analytics capabilities to identify hidden threats and persistent attackers.
- Cloud-based Management Console: The platform is managed through a cloud-based console, providing centralized visibility and control over the entire endpoint security infrastructure. It allows administrators to deploy policies, manage endpoints, and access real-time security insights and reports.
- Next-Generation Antivirus (NGAV): CrowdStrike Falcon leverages artificial intelligence (AI) and machine learning (ML) algorithms to provide superior antivirus protection. It uses behavioral analysis and machine learning models to detect and block malware, ransomware, and other malicious files in real-time.
- Malwarebytes Endpoint Protection is an advanced security solution offered by Malwarebytes, a renowned cybersecurity company. It is designed to protect endpoints, such as desktops, laptops, and servers, from a wide range of cyber threats, including malware, ransomware, exploits, and other malicious attacks. Malwarebytes Endpoint Protection is known for its lightweight footprint and compatibility with existing security solutions, making it suitable for both small and large organizations. It provides an additional layer of defense alongside traditional antivirus solutions and helps organizations strengthen their overall endpoint security posture. Key features and capabilities of Malwarebytes Endpoint Protection include:
- Malware Detection and Removal: The solution uses advanced scanning techniques to detect and remove malware from endpoints. It leverages a combination of signature-based and behavior-based detection methods to identify both known and unknown malware threats.
- Ransomware Protection: Malwarebytes Endpoint Protection provides proactive ransomware protection by monitoring endpoint activities and detecting suspicious behavior associated with ransomware attacks. It can block ransomware encryption attempts and restore files from backup in case of an attack.
- Exploit Mitigation: The solution includes exploit mitigation capabilities to protect endpoints from zero-day exploits and vulnerabilities in popular applications. It monitors system behavior and blocks exploit attempts to prevent attackers from taking advantage of software vulnerabilities.
- Endpoint Isolation: In the event of a compromised endpoint, Malwarebytes Endpoint Protection can isolate the affected device from the network to prevent lateral movement of threats and limit the impact on other endpoints.
- Centralized Management Console: The solution is managed through a centralized management console, allowing administrators to deploy and configure security policies, monitor endpoint status, and generate reports. This provides centralized visibility and control over the entire endpoint security infrastructure.
- Web Protection: Malwarebytes Endpoint Protection includes web protection features to block access to malicious websites, phishing attempts, and other web-based threats. It helps in preventing users from inadvertently visiting malicious websites and downloading infected files.
- Scheduled Scans and Real-Time Protection: The solution offers flexible scheduling options for scanning endpoints to ensure regular and thorough malware detection. It also provides real-time protection, actively monitoring endpoints for malicious activity and blocking threats in real-time.
- Remediation and Quarantine: Malwarebytes Endpoint Protection allows administrators to quarantine and remediate infected files or suspicious items found during scans. It provides options for removing malware or taking appropriate actions to mitigate the threat.
- Malware Detection and Removal: The solution uses advanced scanning techniques to detect and remove malware from endpoints. It leverages a combination of signature-based and behavior-based detection methods to identify both known and unknown malware threats.
- Singularity XDR is developed by SentinelOne, a leading cybersecurity company specializing in endpoint protection and advanced threat detection. Singularity XDR is SentinelOne's comprehensive Extended Detection and Response (XDR) platform. With Singularity XDR, SentinelOne aims to provide organizations with a unified security solution that offers advanced detection, response, and threat hunting capabilities across endpoints, cloud workloads, and IoT devices. The platform leverages AI-powered behavioral analysis and machine learning to detect and respond to sophisticated cyber threats, including malware, ransomware, fileless attacks, and more. SentinelOne's Singularity XDR is designed to empower organizations with advanced endpoint protection, threat detection, and response capabilities. By leveraging AI and automation, it aims to provide holistic security across various endpoints and environments, helping organizations stay ahead of sophisticated cyber threats. Key features of Singularity XDR by SentinelOne include:
- Endpoint Protection: Singularity XDR offers advanced endpoint protection capabilities, providing real-time threat prevention, including malware detection, file integrity monitoring, and vulnerability management. It combines signature-based prevention with AI-driven behavioral analysis to identify and block malicious activities.
- Endpoint Detection and Response (EDR): The platform provides EDR functionality, enabling security teams to detect and respond to security incidents at the endpoint level. It collects rich endpoint telemetry data and performs behavioral analysis to identify suspicious activities, facilitate incident investigation, and support threat hunting.
- AI-driven Threat Hunting: Singularity XDR includes AI-powered threat hunting capabilities, allowing security teams to proactively search for indicators of compromise (IOCs) and potential threats across their environment. It helps identify hidden threats and provides deep visibility into security events to mitigate risks.
- Automated Response and Remediation: The platform offers automated response and remediation actions to quickly contain and mitigate threats. It can automatically isolate compromised endpoints, kill malicious processes, roll back changes, and remediate vulnerabilities to minimize the impact of security incidents.
- Cloud Workload Protection: Singularity XDR extends its protection to cloud workloads, securing virtual machines, containers, and serverless environments. It provides visibility and threat detection capabilities within cloud platforms, allowing organizations to ensure the security of their cloud-based applications and data.
- Threat Intelligence Integration: The platform integrates with external threat intelligence sources, enabling organizations to leverage up-to-date threat intelligence to enhance their detection and response capabilities. It enriches security alerts with contextual information and indicators from external sources for more effective threat analysis.
- Centralized Management and Reporting: Singularity XDR offers a centralized management console for seamless administration and monitoring of security events. It provides comprehensive reporting and analytics features, allowing organizations to generate detailed insights, track key security metrics, and demonstrate compliance with industry regulations.
- Endpoint Protection: Singularity XDR offers advanced endpoint protection capabilities, providing real-time threat prevention, including malware detection, file integrity monitoring, and vulnerability management. It combines signature-based prevention with AI-driven behavioral analysis to identify and block malicious activities.
- ESET PROTECT is a centralized security management platform developed by ESET, a leading cybersecurity company. It is designed to provide comprehensive endpoint protection and streamline the security management process for businesses of all sizes. ESET PROTECT offers a user-friendly interface, scalability, and flexibility to meet the security needs of organizations ranging from small businesses to large enterprises. It provides a comprehensive security management solution that helps protect endpoints, detect threats, and respond to security incidents effectively. ESET PROTECT offers a range of features and functionalities to effectively manage and secure endpoints, including desktops, laptops, servers, mobile devices, and virtual environments. Some key features of ESET PROTECT include:
- Endpoint Security Management: Provides a centralized console for managing and monitoring security across all endpoints within the organization. It allows administrators to deploy ESET security solutions, configure policies, and monitor the security status of endpoints.
- Threat Detection and Prevention: Offers advanced threat detection capabilities, including real-time scanning, behavioral monitoring, and machine learning-based analysis to identify and block known and unknown threats.
- Remote Deployment and Management: Enables remote deployment and management of security solutions, making it easier to protect and manage endpoints across multiple locations or remote environments.
- Policy and Configuration Management: Allows administrators to create and enforce security policies, define application control rules, manage firewall settings, and customize security configurations based on the organization's needs.
- Reporting and Analytics: Provides comprehensive reporting and analytics features, allowing administrators to generate detailed security reports, track security incidents, and gain insights into the overall security posture of the organization.
- Patch Management: Facilitates the management of software updates and patches across endpoints, ensuring that systems are up to date and protected against known vulnerabilities.
- Compliance Monitoring: Helps organizations meet regulatory compliance requirements by providing tools for monitoring and enforcing security policies, conducting security audits, and generating compliance reports.
- Integration and Automation: Supports integration with other IT management tools and systems, allowing organizations to streamline workflows, automate security tasks, and enhance overall operational efficiency.
- Endpoint Security Management: Provides a centralized console for managing and monitoring security across all endpoints within the organization. It allows administrators to deploy ESET security solutions, configure policies, and monitor the security status of endpoints.
- Microsoft Defender for Endpoint, formerly known as Microsoft Defender Advanced Threat Protection (ATP), is a comprehensive endpoint security platform provided by Microsoft. It is designed to help organizations protect their endpoints, such as desktops, laptops, and servers, from a wide range of advanced threats, including malware, ransomware, exploits, and other sophisticated attacks. Microsoft Defender for Endpoint is part of the Microsoft 365 security suite and is available for organizations of all sizes. It combines endpoint protection, detection and response, vulnerability management, and other security capabilities into a unified platform, helping organizations strengthen their overall endpoint security and effectively defend against advanced threats. Key features and capabilities of Microsoft Defender for Endpoint include:
- Endpoint Protection: The solution provides real-time protection against known and unknown threats using various detection and prevention technologies. It leverages machine learning, behavioral analysis, and cloud-based threat intelligence to identify and block malicious activities on endpoints.
- Threat Intelligence: Microsoft Defender for Endpoint benefits from the vast threat intelligence network of Microsoft, collecting data from millions of endpoints and analyzing it to identify emerging threats and attack patterns. This intelligence is used to enhance detection capabilities and provide proactive defense against evolving threats.
- Endpoint Detection and Response (EDR): The EDR capabilities of Microsoft Defender for Endpoint enable security teams to detect and investigate advanced threats on endpoints. It provides detailed visibility into endpoint activities, collects telemetry data, and uses advanced analytics to identify suspicious behavior and potential security incidents.
- Automated Investigation and Remediation: The solution includes automated investigation and response capabilities, leveraging artificial intelligence (AI) and machine learning to investigate and remediate detected threats. It can automatically respond to alerts, isolate compromised endpoints, and remediate malicious files or activities.
- Vulnerability Management: Microsoft Defender for Endpoint helps organizations identify and address vulnerabilities in their endpoints by providing insights into missing security updates and patches. It allows organizations to prioritize and deploy necessary updates to protect against known vulnerabilities.
- Secure Configuration Management: The solution provides security configuration recommendations and helps organizations enforce security baselines on endpoints. It assists in maintaining a secure posture by identifying and remediating insecure configurations that could be exploited by attackers.
- Threat Analytics and Reporting: Microsoft Defender for Endpoint offers rich threat analytics and reporting capabilities, allowing security teams to gain insights into the security landscape of their organization. It provides comprehensive reports on security incidents, threat trends, and overall security posture, helping organizations make informed decisions to improve their security defenses.
- Integration with Microsoft 365 Security Services: Microsoft Defender for Endpoint integrates seamlessly with other Microsoft 365 security services, such as Microsoft Defender for Office 365 and Microsoft Defender for Identity. This integration allows for better correlation of security events and provides a unified view of security across different attack vectors.
- Endpoint Protection: The solution provides real-time protection against known and unknown threats using various detection and prevention technologies. It leverages machine learning, behavioral analysis, and cloud-based threat intelligence to identify and block malicious activities on endpoints.
Security Information and Event Management (SIEM) Solutions
- Splunk Enterprise is a software platform that allows organizations to collect, index, search, analyze, and visualize machine-generated data in real-time. It provides a scalable and flexible solution for processing and gaining insights from vast amounts of data generated by various sources such as applications, servers, network devices, sensors, and more. Splunk Enterprise is widely used across industries for various use cases, including IT operations monitoring, application performance monitoring, log analysis, security monitoring and investigation, business analytics, and more. It helps organizations gain operational intelligence, make data-driven decisions, improve efficiency, enhance security posture, and unlock insights from their data. Key features and capabilities of Splunk Enterprise include:
- Data Collection and Indexing: Splunk can ingest data from diverse sources, including logs, metrics, events, and machine data, and index it in real-time. It supports a wide range of data formats and protocols.
- Search and Analysis: Splunk offers a powerful search language that enables users to quickly search, filter, and analyze data to extract valuable insights. It supports ad-hoc searching as well as complex queries and correlation across multiple data sources.
- Real-time Monitoring and Alerting: Splunk allows users to monitor data streams in real-time, set up alerts based on defined conditions, and trigger actions or notifications when specific events occur. This helps in proactive monitoring and rapid response to critical events.
- Visualization and Reporting: Splunk provides interactive visualizations and dashboards to present data in a visually appealing and meaningful way. Users can create customized reports and dashboards to monitor key performance indicators, track trends, and share insights with stakeholders.
- Machine Learning and Analytics: Splunk integrates machine learning capabilities to automatically detect anomalies, predict future events, and uncover hidden patterns within data. This helps in identifying security threats, performance issues, and operational inefficiencies.
- Security and Compliance: Splunk offers security information and event management (SIEM) functionalities to help organizations monitor and detect security incidents, perform threat hunting, and ensure compliance with regulatory requirements. It can integrate with other security tools and provide a central platform for security operations.
- Data Integration and Extensibility: Splunk provides a wide range of connectors, APIs, and SDKs that enable integration with various data sources, third-party applications, and custom-built solutions. This allows organizations to extend the capabilities of Splunk and integrate it into their existing technology ecosystem.
- Data Collection and Indexing: Splunk can ingest data from diverse sources, including logs, metrics, events, and machine data, and index it in real-time. It supports a wide range of data formats and protocols.
- LogRhythm SIEM (Security Information and Event Management) is a comprehensive security intelligence platform that helps organizations detect, respond to, and mitigate security threats and risks. It collects and analyzes data from various sources across the organization's IT environment to provide real-time monitoring, threat detection, and incident response capabilities. LogRhythm SIEM is designed to enhance an organization's security posture by providing visibility into security events, automating threat detection and response, and supporting compliance requirements. It enables security teams to effectively monitor, investigate, and respond to security incidents, helping protect critical assets and sensitive data. Key features and capabilities of LogRhythm SIEM include:
- Log and Event Collection: LogRhythm SIEM collects and aggregates logs and events from diverse sources such as network devices, servers, applications, endpoints, and security tools. It provides a centralized view of the organization's IT infrastructure and activities.
- Real-time Monitoring and Alerting: The platform continuously monitors the collected data in real-time, applying predefined correlation rules and behavioral analytics to identify security incidents and abnormal behavior. It generates alerts and notifications for potential threats or policy violations.
- Threat Detection and Response: LogRhythm SIEM employs advanced threat detection techniques, including behavioral analysis, anomaly detection, and threat intelligence integration, to identify known and unknown threats. It helps security teams quickly detect and respond to security incidents, minimizing the impact of attacks.
- Incident Management and Workflow: The platform facilitates the workflow and collaboration between security analysts and incident responders. It streamlines the incident investigation process, tracks the progress of incident response activities, and provides case management capabilities.
- Compliance and Reporting: LogRhythm SIEM supports compliance management by collecting and analyzing data to demonstrate adherence to regulatory requirements and industry standards. It provides predefined compliance reports and helps automate compliance workflows.
- Log and Data Analytics: The platform offers powerful analytics capabilities, including log search, data visualization, and behavioral analytics, to gain insights from the collected data. It enables security analysts to identify patterns, trends, and anomalies that may indicate security risks or operational issues.
- Integration and Automation: LogRhythm SIEM integrates with various security technologies, IT systems, and threat intelligence feeds to provide a holistic view of the security landscape. It supports automation through playbooks and workflows, enabling the orchestration of incident response actions.
- Log and Event Collection: LogRhythm SIEM collects and aggregates logs and events from diverse sources such as network devices, servers, applications, endpoints, and security tools. It provides a centralized view of the organization's IT infrastructure and activities.
- QRadar SIEM (Security Information and Event Management) is an enterprise-grade security intelligence platform developed by IBM. It provides organizations with comprehensive capabilities for log management, threat detection, incident response, and compliance management. QRadar SIEM integrates and analyzes data from various sources to detect and respond to security threats in real-time. QRadar SIEM is designed to provide organizations with a centralized and intelligent security monitoring solution. By consolidating and analyzing security events and logs, it helps detect and respond to threats more effectively, improves incident response capabilities, and assists in meeting compliance requirements. Key features and capabilities of QRadar SIEM include:
- Log and Event Collection: QRadar SIEM collects and normalizes log and event data from a wide range of sources, including network devices, servers, applications, security tools, and endpoints. It provides a centralized repository for storing and analyzing this data.
- Real-time Threat Detection: The platform applies advanced analytics, including anomaly detection, behavioral analysis, and correlation rules, to identify potential security threats. It monitors events in real-time, generates alerts for suspicious activities, and helps security teams prioritize and investigate potential incidents.
- Incident Response and Workflow: QRadar SIEM streamlines incident response processes by providing workflows, automated response actions, and collaboration tools. It helps security teams investigate incidents, track the progress of response activities, and ensure timely resolution.
- Threat Intelligence Integration: The platform integrates with threat intelligence feeds, allowing organizations to leverage up-to-date information about known threats and indicators of compromise (IOCs). This integration enhances threat detection and enables proactive defense against emerging threats.
- Compliance Management: QRadar SIEM supports compliance requirements by providing pre-built compliance rules and reports for various regulatory standards. It assists organizations in demonstrating adherence to regulations such as PCI DSS, HIPAA, GDPR, and more.
- Advanced Analytics and Visualization: The platform offers powerful analytics capabilities, including data correlation, user behavior analytics, and visual dashboards. It enables security analysts to gain insights from the collected data, detect complex attack patterns, and visualize security events and trends.
- Integration and Extensibility: QRadar SIEM integrates with a wide range of security technologies, IT systems, and third-party tools. It supports integration with threat intelligence platforms, vulnerability scanners, ticketing systems, and more, enabling organizations to build a comprehensive security ecosystem.
- Log and Event Collection: QRadar SIEM collects and normalizes log and event data from a wide range of sources, including network devices, servers, applications, security tools, and endpoints. It provides a centralized repository for storing and analyzing this data.
- Securonix Next-Gen SIEM (Security Information and Event Management) is a comprehensive security analytics and monitoring platform designed to help organizations detect and respond to advanced threats. It combines security event management, log management, user and entity behavior analytics (UEBA), and threat intelligence capabilities into a unified solution. Securonix Next-Gen SIEM is designed to provide organizations with enhanced threat detection and response capabilities, leveraging advanced analytics and behavioral monitoring. By aggregating and analyzing security data from various sources, it helps organizations identify and respond to security incidents more effectively, reduce risk, and improve their overall security posture. Key features and capabilities of Securonix Next-Gen SIEM include:
- Log and Event Collection: The platform collects and correlates logs and events from a wide range of data sources, including network devices, servers, applications, databases, and cloud environments. It provides centralized storage and analysis of this data to enable real-time monitoring and threat detection.
- Advanced Threat Detection: Securonix utilizes advanced analytics, machine learning, and behavior-based algorithms to identify anomalous activities and potential security threats. It can detect various types of threats, including insider threats, account compromise, data exfiltration, malware infections, and more.
- User and Entity Behavior Analytics (UEBA): Securonix incorporates UEBA capabilities to analyze the behavior patterns of users and entities within an organization's environment. It establishes baselines of normal behavior and alerts on any deviations or suspicious activities that may indicate insider threats or compromised accounts.
- Threat Intelligence Integration: The platform integrates with external threat intelligence feeds, enabling organizations to leverage up-to-date information on known threats, indicators of compromise (IOCs), and malicious actors. This integration enhances threat detection and enables proactive defense against emerging threats.
- Incident Response and Workflow: Securonix facilitates incident response through built-in workflows, case management, and collaboration features. It helps security teams investigate and respond to security incidents efficiently, providing automated response actions and tracking the progress of incident resolution.
- Compliance and Risk Management: The platform supports compliance requirements by providing pre-built compliance reports and dashboards. It helps organizations demonstrate adherence to regulatory standards such as PCI DSS, HIPAA, GDPR, and industry-specific regulations.
- Data Visualization and Reporting: Securonix offers visual dashboards, customizable reports, and data visualizations to provide security analysts and stakeholders with meaningful insights into security events, trends, and risks. It enables easy identification of key security issues and facilitates data-driven decision-making.
- Integration and Extensibility: Securonix supports integration with a wide range of security technologies, threat intelligence platforms, ticketing systems, and other IT systems. This allows organizations to leverage existing security investments and build a comprehensive security ecosystem.
- Log and Event Collection: The platform collects and correlates logs and events from a wide range of data sources, including network devices, servers, applications, databases, and cloud environments. It provides centralized storage and analysis of this data to enable real-time monitoring and threat detection.
- LogPoint is a Security Information and Event Management (SIEM) solution that provides organizations with comprehensive log management, security analytics, and real-time threat detection capabilities. It collects and analyzes log data from various sources across an organization's IT infrastructure to identify security incidents, monitor for suspicious activities, and enable effective incident response. LogPoint SIEM provides organizations with the ability to detect, analyze, and respond to security incidents in real-time. By aggregating and analyzing log data, it enables organizations to gain valuable insights into their security posture, enhance threat detection capabilities, and improve overall security operations efficiency. Key features and capabilities of LogPoint SIEM include:
- Log Collection and Centralized Storage: LogPoint collects log data from diverse sources such as network devices, servers, applications, databases, and security systems. It normalizes and centralizes the log data, providing a unified view of the organization's IT environment.
- Real-time Monitoring and Alerting: The SIEM platform continuously monitors log data in real-time, applying predefined rules, correlation techniques, and behavioral analytics to identify potential security incidents. It generates alerts and notifications when suspicious activities or policy violations are detected.
- Threat Detection and Response: LogPoint leverages advanced analytics, machine learning, and threat intelligence to detect known and unknown threats. It analyzes log data for indicators of compromise (IOCs), anomalous behaviors, and patterns associated with malicious activities. Security teams can investigate and respond to incidents promptly, minimizing the impact of security breaches.
- Compliance Management: LogPoint helps organizations meet regulatory compliance requirements by providing predefined compliance reports, templates, and correlation rules. It supports standards such as PCI DSS, GDPR, HIPAA, ISO 27001, and industry-specific regulations, assisting in audits and demonstrating adherence to security policies.
- Visualization and Reporting: The SIEM platform offers customizable dashboards, data visualizations, and reporting capabilities to provide security analysts and stakeholders with clear insights into security events, trends, and risks. It enables efficient data exploration, drilling down into specific events or timeframes for detailed analysis.
- Integration and Flexibility: LogPoint integrates with various security technologies, network devices, threat intelligence feeds, and IT systems, allowing organizations to leverage their existing security infrastructure. It supports APIs and standard protocols for data ingestion and integration, facilitating seamless communication between different systems.
- Scalability and High Performance: LogPoint is designed to handle large volumes of log data and scales to meet the needs of organizations of all sizes. It offers high-performance indexing and search capabilities, enabling fast retrieval of log data for analysis and investigation.
- Compliance Automation and Case Management: LogPoint automates compliance processes through built-in compliance management features. It helps streamline compliance reporting, track compliance status, and manage compliance-related tasks. The platform also includes case management capabilities to facilitate incident response workflows and collaboration among security teams.
- Log Collection and Centralized Storage: LogPoint collects log data from diverse sources such as network devices, servers, applications, databases, and security systems. It normalizes and centralizes the log data, providing a unified view of the organization's IT environment.
References:
https://www.gartner.com/reviews/market/network-firewalls
https://www.gartner.com/reviews/market/endpoint-protection-platforms
https://www.cisco.com/c/en/us/products/security/what-is-network-security.html
https://www.gartner.com/reviews/market/security-information-event-management