Exploit Database (Exploit-DB) is a widely recognized online repository that provides a collection of security vulnerabilities, exploits, and related tools for various software applications, operating systems, and devices. It serves as a valuable resource for security researchers, penetration testers, and cybersecurity professionals seeking information about vulnerabilities to better understand, mitigate, and protect against potential threats.
Key Benefits of Exploit-DB
- Vulnerability Awareness: Exploit-DB helps security professionals stay informed about the latest security vulnerabilities in a wide range of software, enabling them to take proactive measures to secure systems.
- Educational Resource: Researchers, students, and enthusiasts can use Exploit-DB to learn about various attack techniques, vulnerabilities, and exploit methods.
- Penetration Testing: Penetration testers and ethical hackers can utilize exploit code available in Exploit-DB to assess the security of systems and applications, identifying potential weaknesses.
- Response and Mitigation: Organizations can use Exploit-DB to identify vulnerabilities affecting their systems and take steps to patch or mitigate those vulnerabilities.
- Research and Analysis: Security experts can analyze exploit code to understand attack vectors, potential impacts, and how to defend against specific vulnerabilities.
- Legal Exploration: Exploit-DB provides a platform for legally and ethically exploring vulnerabilities and exploit techniques, contributing to responsible security research.
Key Features of Exploit-DB
- Searchable Database: Exploit-DB offers a user-friendly interface that allows users to search for vulnerabilities, exploits, and related information using keywords and filters.
- Comprehensive Information: Each entry in Exploit-DB includes detailed information about the vulnerability, affected software, potential impact, and any relevant references.
- Exploit Code: Many entries include actual exploit code that demonstrates how a vulnerability can be exploited, aiding researchers and testers in understanding the attack vector.
- Platform Coverage: Exploit-DB covers vulnerabilities across a wide range of platforms, including different operating systems, applications, and devices.
- Metasploit Integration: Some entries are integrated with the Metasploit Framework, a widely used penetration testing tool, making it easier to use the exploits.
- Categorization and Tagging: Vulnerabilities and exploits are categorized and tagged based on their nature and characteristics, facilitating easy navigation and discovery.
- Contributions and Community: Security researchers can contribute their findings and exploit code to Exploit-DB, fostering community collaboration and sharing of knowledge.
- Historical Records: Exploit-DB maintains a historical record of vulnerabilities and exploits, enabling users to track the evolution of security issues over time.
- Regular Updates: The database is regularly updated with new vulnerabilities, exploits, and related information to ensure that the content remains current.
While Exploit-DB is a valuable tool for security professionals, it's important to use it responsibly and in accordance with ethical guidelines. Unauthorized or malicious use of exploit code is illegal and unethical.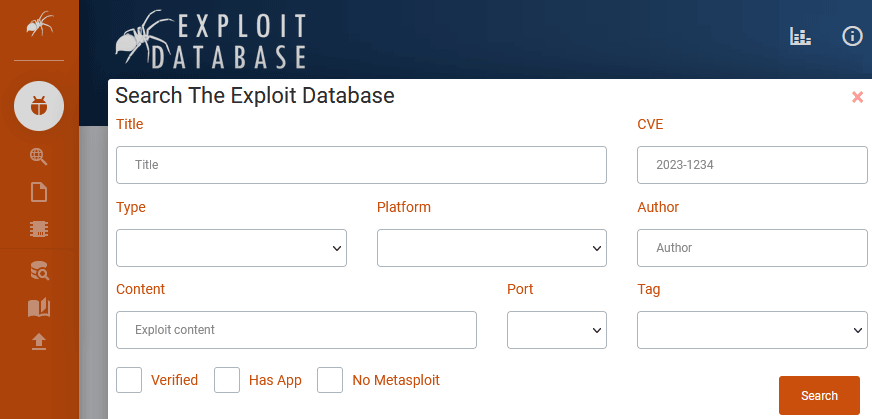
Exploit-DB offers the following:
- Exploits Database
https://www.exploit-db.com - Google Hacking Database
https://www.exploit-db.com/google-hacking-database - Exploit Database Shellcodes
https://www.exploit-db.com/shellcodes - SearchSploit
https://www.exploit-db.com/searchsploit
For more information about CloudGoat, visit the following link:
https://www.exploit-db.com/about-exploit-db